This article is more than 1 year old
NASA reports first sighting of dry ice Martian snowfalls
Carbon-dioxide flakes form and fall
Scientists using the Mars Reconnaissance Orbiter have found definitive proof that flurries of carbon-dioxide snow are falling on the Martian South Pole.
"These are the first definitive detections of carbon-dioxide snow clouds," said Paul Hayne of NASA's Jet Propulsion Laboratory in a statement. "We firmly establish the clouds are composed of carbon dioxide - flakes of Martian air - and they are thick enough to result in snowfall accumulation at the surface."
The seven-person team used data from the Mars Climate Sounder onboard the MRO satellite to examine the snow clouds both from above, but also from the side. The instrument scans across nine points of the visible and infrared ranges of the electromagnetic spectrum to detect atmospheric composition.
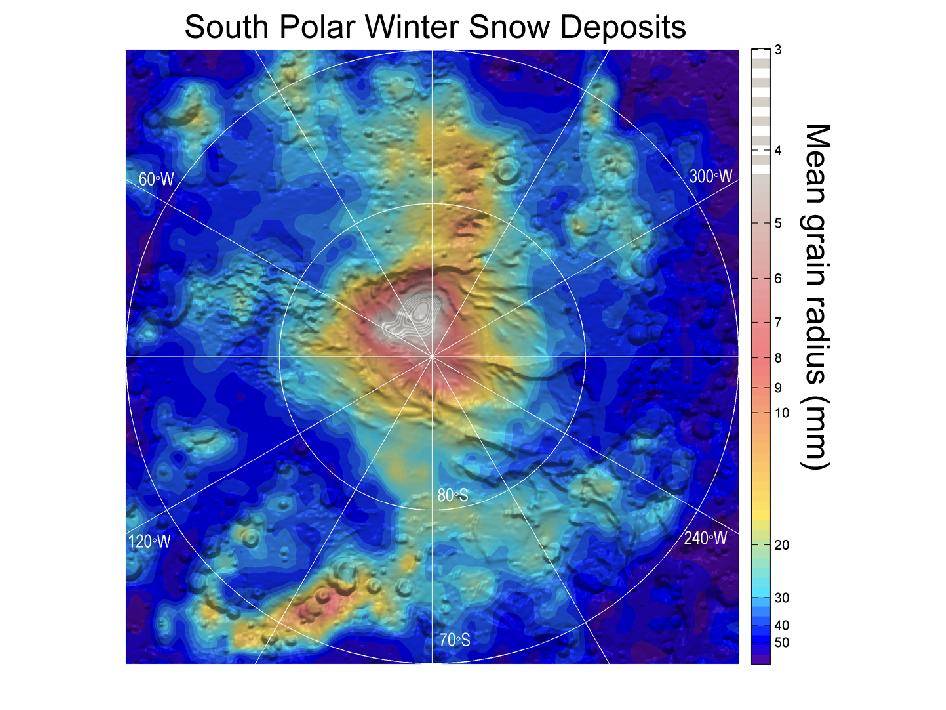
The snow-bearing clouds were scanned during southern Mars winter in 2006-2007, when a 300-mile diameter cloud hung over the South Pole and shed its load via several smaller cloud systems. The resulting map shows exactly where on the southern pole the carbon accumulates in flaked form.
NASA's Phoenix lander reported seeing water vapor falling as snow back in 2008, although it didn’t survive reaching the Martian surface. This is the first time carbon dioxide has been spotted in solid form on the Red Planet, and although no precise images of the flakes falling exist, the evidence it there to show them in action NASA says.
"One line of evidence for snow is that the carbon-dioxide ice particles in the clouds are large enough to fall to the ground during the lifespan of the clouds," co-author David Kass of JPL said. "Another comes from observations when the instrument is pointed toward the horizon, instead of down at the surface."
"The infrared spectra signature of the clouds viewed from this angle is clearly carbon-dioxide ice particles and they extend to the surface. By observing this way, the Mars Climate Sounder is able to distinguish the particles in the atmosphere from the dry ice on the surface." ®