This article is more than 1 year old
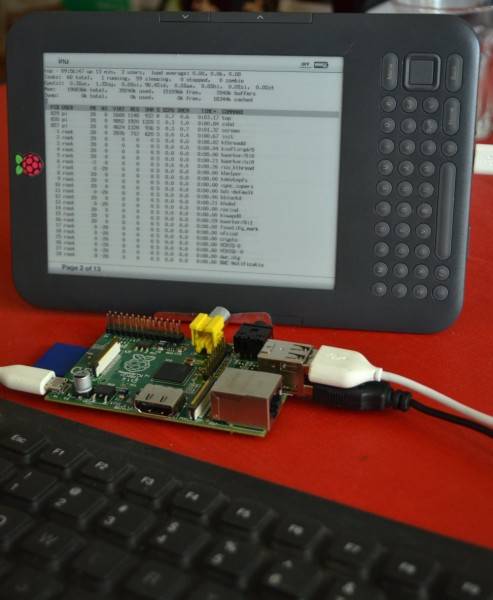
Hacker uses Kindle as Raspberry Pi screen
DIY instructions await the brave or foolish
A hacker named Gef has rigged up his Raspberry Pi to use a Kindle e-reader as its monitor.
“Hacker” may not quite be the word, actually, as the individual responsible identifies himself as an “eclectic yogi discovering the world of computational art and new media” on the blog post where the recipe for the KindleBerry Pi is revealed. Names aren't the guy's long suit either: his Twitter account says he's called “Gef” although his handle is @damarusama.
We'll nonetheless proceed on the basis this is the work of a human, not a canine, and report that the way to achieve the feat of using a Kindle as a Pi's monitor requires you to:
"Jail break the Kindle, install this terminal emulator … and then install UsbNetwork. Make sure the usbNetwork is enable, Connect the devices through USB, do a quick ifconfig usb0 192.168.2.1 and Voila … login into the Raspberry Pi with no problem."
At this point it is apparently possible to use the Kindle's keyboard to control the Pi, but as the display operates in landscape mode the keyboard is at a 90 degree angle to the screen. That's hard enough to manage without the nasty nature of the Kindle's keyboard, so Gef recommends using a USB keyboard.
That turns out to be a non-trivial task as installing the USB keyboard can't be done without first entering some commands with the Kindle's keyboard.
While the rig worked, Gef eventually figured out it wasn't very practical.
"I quickly realized that if I wanted to do anything productive at this point it was better to get myself a computer," Gef wrote. Feel free to disagree. ®
