This article is more than 1 year old
Ivy Bridge for Ultrabooks
Inside Intel's premium portables
The one thing missing at the launch of Intel’s Ivy Bridge CPU technology was detail on the dual-core and lower powered chips for the mobile market segment, in particular, for its Ultrabook concept. The recent launch of the ULV (Ultra Low Voltage) and dual-core standard voltage mobile Ivy Bridge parts has revealed all, with the ULV parts being of particular interest to Ultrabook manufacturers.
To put the latest technology through its paces, I have an Intel badged Ultrabook – it must be, it says so on the lid – but before you rush down to the shops to try to put in an order for it, don’t bother. It’s not a retail product, just a proof of concept to tout the new mobile Ivy Bridge technology and show how a second generation of Ultrabook might perform. Early signs suggest some very nice kit will see the light of day in the coming months.
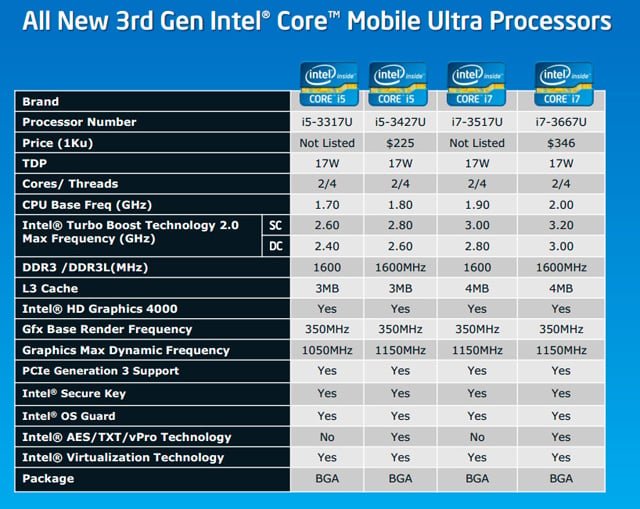
Intel Ivy Bridge Core i mobile Ultra processors roadmap
Before I get into the Ivy Bridge Ultrabook experience, let's take a look at the mobile processors available for this third generation Core i-series. The new ULV (Ultra Low Voltage) CPUs are dual-core, four thread 22nm processors.
The current line-up features of two Core i7 offerings: the flagship i7-3667U (2.0GHz base clock, 3.2GHz single core Turbo, 3.0GHz dual-core Turbo) and the i7-3517U (1.9GHz base clock, 3.0GHz single-core Turbo, 2.8GHz dual-core Turbo). The two Core i5 chips are the i5-3427U (1.8GHz base clock, 2.8GHz single-core Turbo, 2.6GHz dual-core Turbo) and the i5-3317U (1.7GHz base clock, 2.6GHz single-core Turbo, 2.4GHz dual-core Turbo).
All four ULV CPUs have a TDP of 17W, with the two Core i7s having 4MB of L3 cache, while the two Core i5s have 1MB less at 3MB. All support a maximum memory speed of DDR3-1600 and all use Intel’s HD4000 GPU graphics clocked at 350/1150MHz – the exception being the i5-3317U which is limited to a maximum of 1050MHz. For business users, the i7-3517U and i5-3317U processors might be the ones to avoid as they have neither vPro nor Intel Trusted Execution Technology support.
