This article is more than 1 year old
Ten freeware gems for new Macs
Complimentary benefits
Carbon Copy Cloner

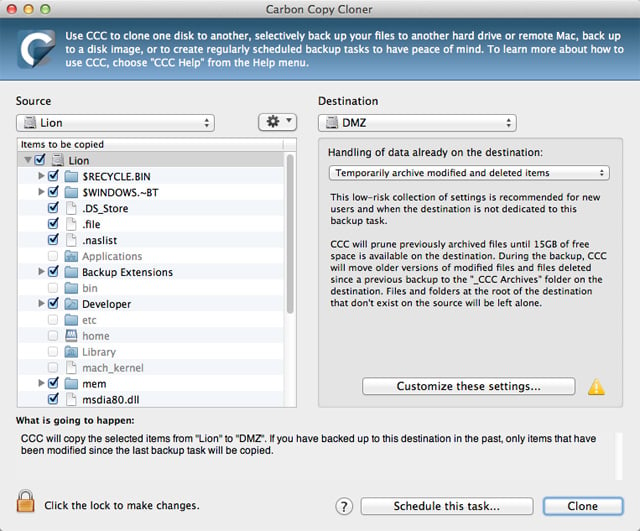
For most people, TimeMachine will be a sufficient backup system, but if you want to have a little more power over your data protection, Carbon Copy Cloner is a fantastic tool. You can create fully bootable backups – in essence, you can author a full operating system backup.
Network, scheduled and sequential backups can also be performed and you can even use the data with Migration Assistant. This is an invaluable tool for system admins who need to deploy identical Mac OS X installations with ease and even direct disk-to-disk block-level cloning is supported.
More info CCC
Deeper

While most aspects of Mac OS X can be tweaked somewhat, Deeper opens up a new world of possibilities. Modifications can be made to the Dock, Finder, Spotlight and Login screen, but the fun doesn’t end there. Also alterable are Safari, Mail, QuickTime and iTunes.
Most tweaks are of a visual or organisational nature, but there are also hidden features to be unlocked in several areas. Deeper is an absolute must-have for users who spend hours customising their OS after a clean instal. Check it out; you might discover your Mac can do something you didn’t know about.
More info Deeper


