This article is more than 1 year old
Greenland melt surprises NASA Earth-watchers
Giant slushy attributed to ‘heat dome’
Repeated ridges of warm air passing over Greenland since May have induced what NASA says is the largest surface melt in the mostly-frozen island in the age of satellite observations.
The once-in-150-years surface melt – which will, it’s important to note, still leave most of the huge 3.2 km centre ice sheet in place – took place over just four days beginning July 8. According to NASA’s JPL, “nearly the entire ice cover of Greenland … experienced some degree of melting at its surface” in that short period.
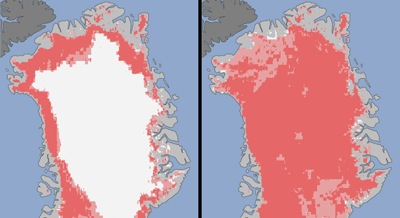
Greenland in July: Dark pink areas show melting confirmed by two or more observations,
while pale pink areas indicate melting observed by one satellite.
The left-hand image is from July 8, the right-hand July 12.
Image: Jesse Allen, NASA Earth Observatory and Nicolo DiGirolamo,
SSAI and Cryospheric Sciences Laboratory
JPL isn’t attributing this event to climate change, but rather to a predictable cycle in Greenland’s weather. "Ice cores from Summit show that melting events of this type occur about once every 150 years on average. With the last one happening in 1889, this event is right on time," said Lora Koenig, a glaciologist at NASA’s Goddard Space Flight Center.
However, she added that repeated similar melts in the near future would be “worrying”.
According to NASA, the first observations – noted in an analysis of data from India’s Oceansat-2 – were so startling that a data error was suspected, but the Indian information was confirmed by MODIS data from NASA’s Terra and Aqua satellites.
Further confirmation came from the University of Georgia and City University of New York, where Thomas Mote and Marco Tedesco repectively confirmed the Oceansat-2, Terra and Aqua observations with the US Air Force’s Special Sensor Microwave Imager/Sounder satellite.
The analysis showed that by July 8, the melt covered 40 percent of Greenland’s surface ice, rising to 97 percent by July 12. The heat dome fingered as the cause of the melt began arriving on July 8, parked itself for three days, and finally started dissipating by July 16. ®
