This article is more than 1 year old
Google asks YouTube commenters to stand up and be counted
New option asks for user's ID
Google has altered the comments system on YouTube to encourage those who wish to share their views to step up and identify themselves.
Under the new system anyone trying to leave a comment on YouTube will be asked if they would like to identify themselves using a Google+ account. It's not compulsory, but those that decline this option are shown a new page asking why they chose to remain behind a cloak of anonymity.
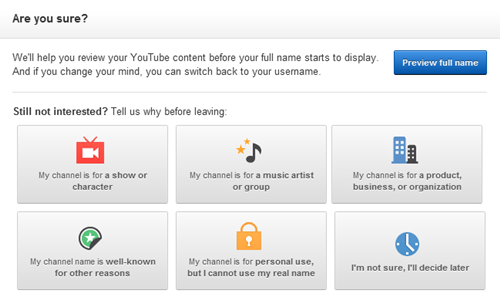
Sadly no "Because I'm an immature coward" option
There's also an option to backdate the identification option to past posts, but this can be applied selectively if you don't want to assign your name to that drunken comment about President Obama's birthplace.
Having commentators identify themselves should make them think a little bit more about what they write, but the changes are unlikely to bring about any serious cleanup of the site's commentary zone, since it's not compulsory. That said, the new query pages could get annoying enough after a while to encourage the flamers to move on.
YouTube has long been recognized as having one of the noisiest and rambunctious user commentary areas, where politeness is a collection of syllables and Godwin's Law just a suggestion. Internet court jester Randal Munroe even suggested an elegant application fix for the YouTube comments problem. ®
