This article is more than 1 year old
Buy Smarter: what you need to know about... optical disc drives
Laser sharp storage
Buyer's Guide Optical drive is the collective term for CD, DVD and Blu-ray readers, recorders and rewriters, the mainstay of swap-in-swap-out storage in notebook and desktop computers.
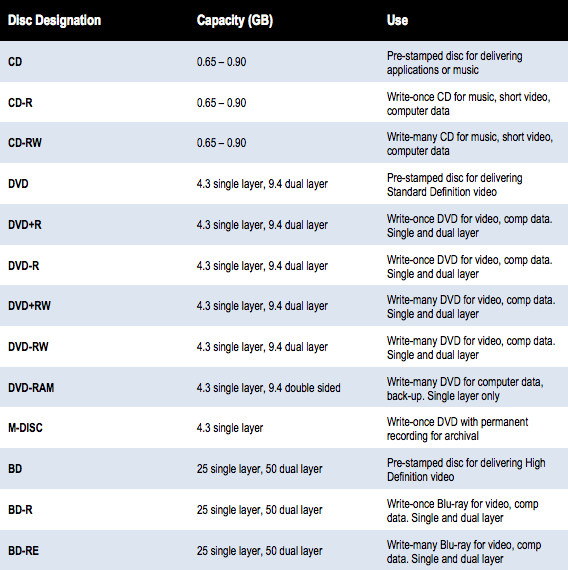
At its simplest, an optical disc can load applications or play music or films, and at its most complex, in the form of a dual-layer, Blu-ray BD-RE disc, it can play high-definition (HD) movies and record up to 50GB of data.
You may be wanting to upgrade an optical drive, or move from CD to DVD or DVD to Blu-ray, or you may want to add an extra drive to a machine with a spare bay. Whatever it is, there is a variety of drives to choose from.
Optical drive types
You will find it increasingly difficult to buy a CD-only drive, as effectively all DVD drives play all varieties of CD in addition to handling a range of DVD types. Blu-ray drives can similarly read, and usually write, both DVDs and CDs.

Upgrade your desktop's internal optical drive for greater capacity storage and HD playback
There is only one type of recordable and one type of rewriteable CD, but there are two complementary standards of DVDs: DVD+R/RW and DVD-R/RW. These DVD-plus and DVD-minus formats are distinct, but most modern drives can read and write both of them.
The rewriteable Blu-ray drive uses the abbreviation BD-RE, rather than BD-RW, as the drive has to be fully Erased before rewriting.
DVD drives are available as standard 3.5in internal and half-height, laptop-style devices. Both of these can also be had as external drives in separate enclosures, linked via USB, Firewire or eSATA cables.The Samsung Ultra-Slim AA-ES3P95B charges easily using one USB cable and has a hidden power cord. If you are after an external drive, make sure you get the appropriate type for the connection you have available.
Optical Disc Formats