This article is more than 1 year old
AMD and Intel mainstream desktop CPUs
Cheap as chips?
Intel Core i3-2105
Intel’s Core i3-2105 is a 3.1GHz dual-core CPU with hyper threading, so any OS will see it as a four-core processor, although it’s not as efficient when it comes to multithreaded jobs as a true quad core processor, such as the AMD A8-3870K. Although, just like the A8-3870K, it lacks a Turbo boost to dynamically increase the clock speed, should the need arise. The Intel Core i3-2105 also has its multipliers locked, so any overclocking can only be done via the system bus, which limits what can achieved.
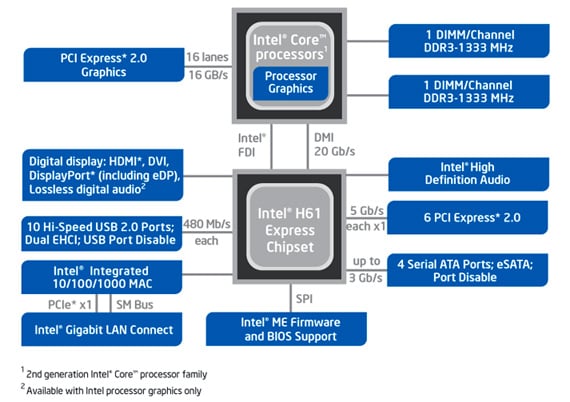
Intel H61 Express chipset block diagram
The desktop versions of the Core i3 normally use the HD2000 version of Intel’s integrated graphics core but the i3-2105 was the first member of the family to use the more powerful HD3000 graphics core which, at the time of its release, was only to be found in some Core i5 and i7 CPUs.
Benchmark Tests
PCMark7 overall score
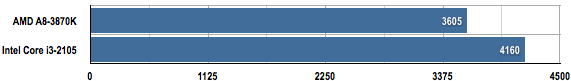
Longer bars are better
Cinebench R11.5 Index Score
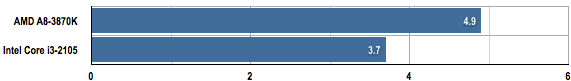
Longer bars are better
AMD and Intel X264 V4.0 video encoding rate
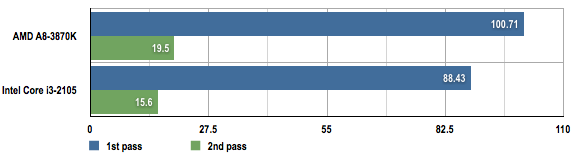
Average frame rate: longer bars are better
Verdict
When it comes to the mainstream market for CPUs, the phrase, "You’ve never had it so good” springs to mind. With a multitude of processors to choose from and priced such that there is a CPU for every budget. If it’s confusing now it’ll only get worse when the low-end Ivy Bridge processors eventually turn up. The good news is that, if you don’t want to go down the Intel path, there are plenty of respectable and affordable options available from AMD that have some unique and innovative features on-board too. ®
