2
This article is more than 1 year old
Scaling the heights of private cloud
Take me, take me to the top
Infographic We’ve done it again. Another couple of slices through our Private Cloud research delivered in stunning Technicolor gloryvision.
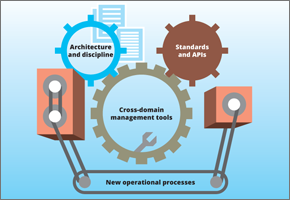
 For this beauty, click the pic to see it (PDF), we’ve zoomed in on the route from virtualisation to private cloud, showing adoption, how challenges are tackled, the progress made by your peers. And the necessary steps they've taken on the journey.
For this beauty, click the pic to see it (PDF), we’ve zoomed in on the route from virtualisation to private cloud, showing adoption, how challenges are tackled, the progress made by your peers. And the necessary steps they've taken on the journey.
This one on the other hand, is your cut-out-and-keep guide to running a hybrid cloud infrastructure. Click the pic (PDF).