This article is more than 1 year old
Gigapixel camera heralds new world of snoopery
You want detail? We got detail
If you listen very carefully, you can hear the owners of high-end digital SLRs yelling “I want it!” at their computer screens: Duke University researchers have stitched together 98 “microcameras” into a 50-gigapixel monster called AWARE 2.
As the researchers note in their paper in Nature (abstract here), “Ubiquitous gigapixel cameras may transform the central challenge of photography from the question of where to point the camera to that of how to mine the data.”
AWARE 2’s resolution is described as “five times better” than the resolution humans with 20/20 vision have.
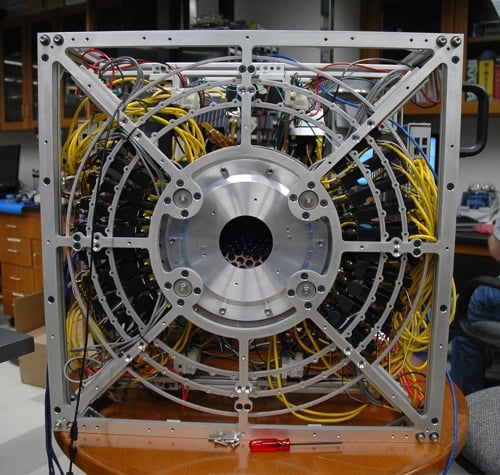
Duke U's gigapixel behemouth
Rather than improve the optics of the camera, the researchers focused on the electronics: its 120-inch horizontal field is made of 98 individual “microcameras” each with a 14 megapixel sensor. The optics is fairly straightforward by comparison: one objective lens, with micro-lenses routing different components of the field of view to individual microcameras.
These individual images are then assembled into a single image using software.
The full spec of AWARE 2 can be found here, with a bunch of example images here. Rather than spoil the experience by trying to clip out an image, El Reg suggests readers take a look at the pic entitled “Looking Across the Atrium”, with particular attention to the resolution gauge taped to the wall away from the camera.
AWARE 2 is hardly “ready for prime time”: it’s large and heavy, with much of its bulk devoted to keeping the electronics cool. However, Duke’s researchers believe that gigapixel cameras could be a viable product within five years.
The team of 50 students, researchers and engineers included contributions from the University of California San Francisco, as well as industrial partners from Rochester Photonics and Moondog Optics. ®
