This article is more than 1 year old
AMD and Nvidia extreme GPUs workout
Visual feast
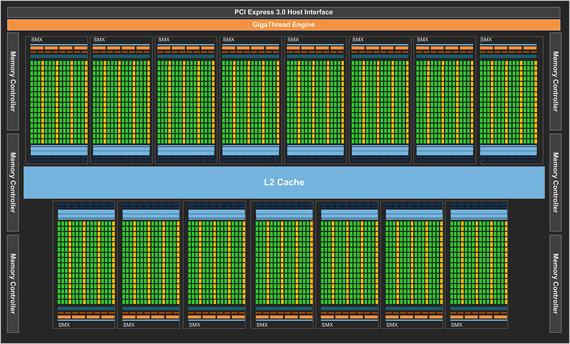
Nvidia Kepler
Kepler’s predecessor was codenamed Fermi and it’s an understatement to say that it had a difficult birth. Still, all credit to Nvidia though, it stuck with Fermi and turned out some very good graphics cards with later incarnations of the architecture. A feat that a great number of people thought impossible having played around with the first examples of it. Not wishing to make the same mistake twice, the Nvidia took its time to unleash Kepler. Time, that was presumably well spent keeping an eye on what AMD was doing with its 7000 series.
Like AMD’s Southern Island’s architecture, Kepler is built using a 28nm process but is a much smaller chip at just 295mm², but then it does have a lower transistor count at 3.5 billion.
Furthermore, it’s not strictly a totally new architecture either, but more of a Fermi die shrink, tidy up and update. The upshot is its leaner, meaner and more power efficient processor. The first example of the new architecture to see daylight carries the codename GK104 but is better known as the GeForce GTX 680.
The GTX 680 has 1536 CUDA cores which is a staggering three times as many as the previous generation’s GTX 580. This massive rise is due to the fact that Nvidia has junked the shader clock and chosen to increase the number of CUDA cores to achieve the same effect.
Albeit minus the shader clock, Nividia has added a Boost Clock, so although the base clock speed is 1006MHz, the boost speed – turbo, if you like – is 1058MHz. The 2GB of GDDR5 memory is clocked at 6.008GHz and runs through a 256-bit bus giving a maximum memory bandwidth of 192.4GB/sec. So technically, that’s the how the land lies between these two gods of graphics, but back in the real world, how do these architectures fare in products you can actually buy?