This article is more than 1 year old
EMC rounds up rival arrays, beats 'em into submission
You will work with each other
EMC VMAX arrays will team up competing drive arrays with a new version of the VMAX Enginuity OS.
Much like the existing HDS VSP and NetApp V-Series, Enginuity v5876 will enable VMX to virtualise third-party arrays behind a VMAX head using EMC Symmetrix Federated Tiered Storage (FTS). The VMAX, which is getting a substantial makeover, sees them as physical disk space.
An EMC white paper [PDF] states: "This permits the user to manage, monitor, migrate, and replicate data residing on both Symmetrix and non-Symmetrix arrays using familiar EMC software and Enginuity features" - such as SRDF, TimeFinder and VMAX Virtual Provisioning.
The white paper uses an HP XP24000 as an example third-party array adopted or corralled by VMAX. LUNS stored on the XP24000 are used to provide raw storage space for VMAX. These LUNS are called eDisks and are Symmetrix devices, just like internal VMAX disk drives.
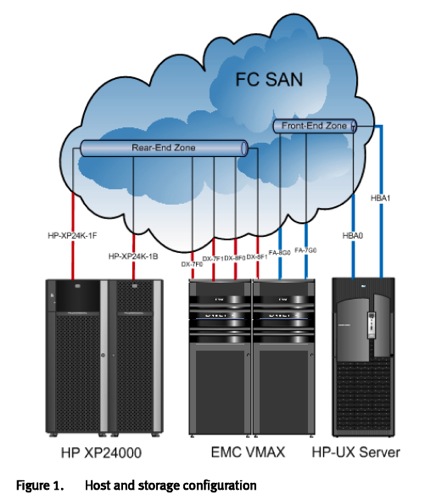
VMAX virtualising an HP XP24000
The external arrays are connected to VMAX by Fibre Channel. In an EMC Labs exercise a HDS-USP array, which is practically what HP OEMed as its XP240000, stored an Oracle 11g database accessed by a primary HP UX server host and various HP server secondary hosts running Windows, Solaris and ESX.
These hosts were moved to a VMAX 40K, the refreshed VMAX expected to feature at EMC World, and the USP hooked up to a VMAX using Fibre Channel. Then the HDS volumes were made available to the moved hosts through VMAX volumes and eDisks using an encapsulation feature. See the white paper above for more details.
No doubt EMC will produce a list of compatible third-party arrays at announcement time. With the USP supported we could, if we are mischievous, envisage a VMAX 40K virtualising a USP-V which virtualises a NetApp V-Series which virtualises a VMAX, completing the circle and wasting an enormous amount of IO connectivity to have virtualised storage chasing its own tail. ®
