This article is more than 1 year old
Tablets are the future of the PC, says researcher
Fondleslabs to eat into laptop sales, boost desktops
Ask Frank Gillett, a researcher with market watcher Forrester, whether tablets are going to dominate how people interact with content and the internet - what most folk do with laptops and such - and the answer is a resounding 'yes'.
He reckons that "tablets will become the preferred, primary device for millions of people around the world" as users come to appreciate their advantages.
"Tablets aren’t the most powerful computing gadgets," says Gillett, "but they are the most convenient. They have longer battery life and always-on capabilities better than any PC — and will continue to be better at that than any ultrathin laptop," he says, enumerating tablets' virtues.
"That makes them very handy for carrying around and using frequently, casually, and intermittently even where there isn’t a flat surface or a chair on which to use a laptop."
But what about the old content consumption and creation dichotomy? Says Frank: tablets are great for the former, but they'll get into the latter as developers code creative apps for them.
"They’ll get a lot better as developers get used to building for touch-first interfaces, taking advantage of voice input, and adding motion gestures," he says.
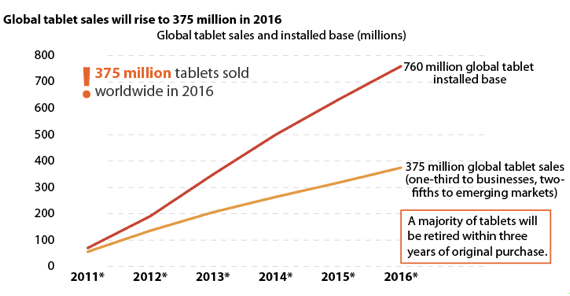
Source: Forrester Research
Not that the PC is going away. Gillett forecasts that some two billion laptops and desktops will be in use by 2016. Tablets will eat into PC sales for sure, but only partially.
In fact, they'll actually help desktop sales, Gillett believes, with punters - "especially information workers", he says - opting for a powerful stationary machine for creative work and content management, and a tablet for accessing that content in a convenient way.
In the meantime, tablet sales will rise year on year, hitting 375m in 2016, up from 56m in 2011. Come 2016, the installed base of tablets will be in the region of 760m units, Gillett says. That amounts to almost 40 per cent of the installed base of PCs by then. ®
