This article is more than 1 year old
Turing's rapid Nazi Enigma code-breaking secret revealed
Maths homework kept in GCHQ vault for 70 years
Blighty's communications eavesdropping nerve centre GCHQ has issued two papers written by superboffin Alan Turing on the maths behind code-breaking.
The documents, held in secret for 70 years, laid the foundations for the quick and efficient decryption of Nazi Enigma-scrambled messages - a breakthrough that lopped about two years off the duration of the Second World War.
The papers were donated on Friday to The National Archive in Kew, Surrey, where they will be available to view on request. An archives spokesperson said demand to see Turing's work is high, but there is no plan to put it online.
The GCHQ mathematician who handed over the documents, named only as Richard, told the BBC that the agency had now "squeezed the juice" out of the two papers and was "happy for them to be released into the public domain". The move coincides with the 100th anniversary of Turing's birth on 23 June this year.
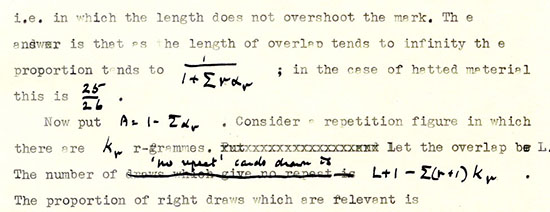
The two typewritten papers feature Turing's hand-scribbled notes, and are titled On Statistics of Repetitions and The Applications of Probability to Cryptography.
The statistics paper describes how examining repeated characters in two encrypted messages can prove that both passages use the same encipherment key. The cryptography essay is longer and applies rigorous probability analysis to code-breaking methods and techniques.
The mathematical workings are given a little historical piquancy when Turing uses life expectancy to examine conditional probability, taking Hitler - then aged 52 - as an example. It dates the paper to between April 1941 and April 1942.
According to GCHQ's Richard, the papers used "mathematical analysis to try and determine the more likely settings [for the crypto key] so that they can be tried as quickly as possible".
The agency added that the message decryption rate achieved by wartime code-breakers at Bletchley Park was "almost certainly enabled by the techniques in this paper". More details on Turing's newly revealed work can be found here. ®