This article is more than 1 year old
Lytro light field camera
Shoot first, focus later
Soft touch
The real cleverness of the Lytro camera lies in its software, as it’s a simple looking device. There are only two buttons, one on the top which turns the camera on and works the shutter and one on the bottom which turns the camera on and off.

The screen size makes it difficult to judge your shots
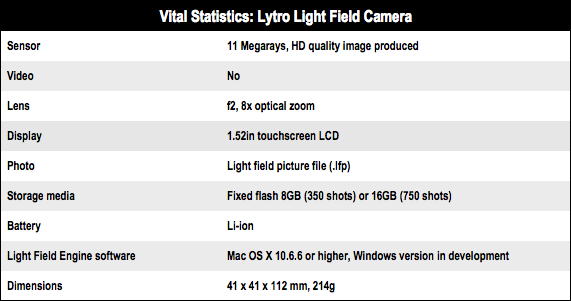
The battery is not removable, and neither is the storage. It comes in 8GB and 16GB configurations, the larger one only in red, the smaller one in graphite and blue. Lytro claims a 16GB camera will hold 750 images, in use I found it nearer to 500.
Given there is no focus, consequentially it has no aperture control. Nor is there control over shutter speed. The only controls are an optical zoom which is hidden in a touch sensor along the patterned rubber top and a touch screen.

Concealed micro USB connection
Under a flap there is a micro-USB connector. The screen gives a few controls, you can use it to view pictures, and tap to focus on a picture, mark some pictures as favourites, and put the camera into “creative mode”.
The creative mode lets you stipulate the centre of the focus for the spread of focal points, so this image uses the automatic setting...
...while the image below had the centre of focus stipulated as between the nurse and the knights using creative mode.
You’ll see that in the second picture the back row of people can’t be brought into focus.
Alas, the screen is dreadful. It’s too small and of too low a resolution to see any detail in the pictures. It’s not really possible to see the effects of the focus unless they are really marked. In bright light, it is worse and you have to just snap and hope. What it really needs is a USB link to a tablet – a latest generation iPad would be ideal – so that you can see the pictures, and one is in the works, apparently.