Twisted thinking
Away from cutscenes the single-player options consist of a series of arena battles which are essential solely because it's from their completion that you unlock the game’s extra vehicles and weapons. Alas, these missions feel like an unnecessary grind. The AI-driven cars are simply not varied enough in their play to really entertain and the upshot is strain on your patience.

Masked intent
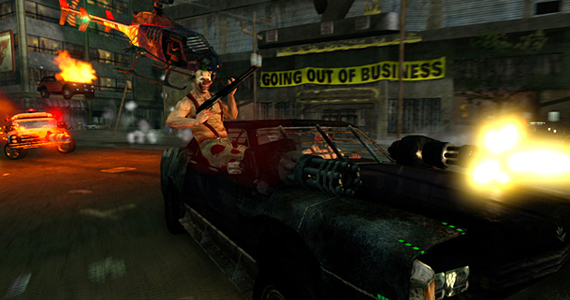
Then there are those visuals which might be said to be functional, at best. Yes it's possible to ram straight through buildings – though only certain parts of them – and unleash hell at the click of a button, but never is there a stop-and-stare moment to behold, nor a crunching blow followed by a suitably show-stopping visual response to really savour.
At least the solo missions can be used to learn the layouts of the multi-storied arenas, which hold any number of secret pick-ups. For instance, Vertigo takes place across the tops of LA’s skyscrapers – cue much shunting of your fellow drivers off the sides – while the backwater town of Sunsprings, California has numerous homes and even a church all containing munitions secreted away.

Transformed character
Arenas can also be played over a variety of game types. Deathmatch is the traditional kill-or-be-killed formula we know so well. Hunted is a glorified game of tag and then there’s a take on Capture the Flag called Nuke, where the enemy's leader must be chained to a missile before being blasted at a Statue of Liberty type effigy.
Finally, there is Last Man Standing, which bestows each player with a number of lives which have to be preserved if you’re to win. Not so easy to do when faced with 16 players looking to do likewise.
Buster cap
For those not au fait with the rudimentaries of Twisted Metal's moves and controls, each car is able to perform a variety of stunts. Turbo boosting is your meat and drink – perfect for ramming unwary opponents – while jumping can help you clear obstacles. Each car also has access to constantly regenerating shields and immobilising freeze blasts, while vehicles – regardless of size or number of axles – are all able to turn on a sixpence at the touch of the handbrake.
