This article is more than 1 year old
Panasonic CF-53 Toughbook 14in rugged laptop
A bit of a hard case
Drop box?
I then knocked the CF-53 Toughbook off my dining room table onto the carpeted floor to see if the shock protected HDD can take a punch. It can. I could have been more brutal but I want Panasonic to lend me one of its toughened Android tablets next month and handing the CF-53 Toughbook back in bits would most likely jeopardise that. Also the CF-53 Toughbook is supposed to cater for users who are active and mobile, not clumsy and stupid.

Lugs cover the interfacing apart from the audio jacks at the front
To prevent the ingress of dust or moisture all the CF-53’s ports apart from the 3.5mm audio and microphone jacks at the front are covered by flaps. The doors aren’t watertight but seem more than capable of keeping building site detritus and the like at bay.
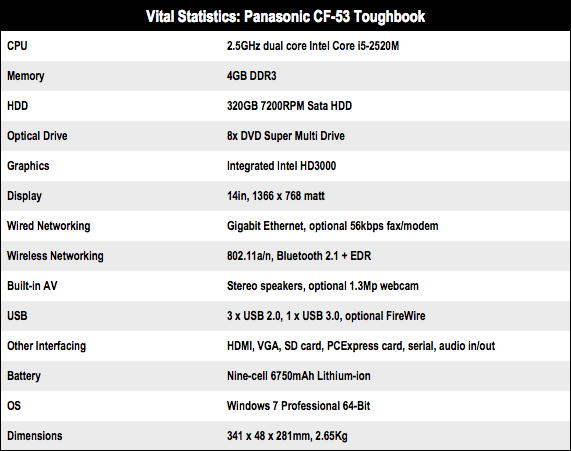
The right-hand side of the CF-53 houses a USB 2.0 and USB 3.0 port, a SD card reader, ExpressCard slot, power jack and a compartment for the 6750mAh Lithium-ion battery. A DVD burner occupies the left side while two USB 2.0 ports, Ethernet, VGA, HDMI and serial ports live around the back. Flip the machine onto it’s back and the covers for the WLAN, memory and HDD bays are all easily removable, the last without even needing a screw driver.

Pit stop style parts swap
Oddly for a machine designed to be used out of the office, a webcam is an optional extra. I’d have thought the ability to quickly video-call support staff using Skype would be a vital feature for this sort of machine.

The 2.5GHz Core i5 CPU in this model is getting on a bit now
Inside you will find a 2.5GHz Intel Core i5-2520M CPU with 4GB of RAM running Windows 7 Professional. That means it runs just like all the other hundreds of similarly specified laptops made since this Core i5 chip appeared about a year ago, and like them it is no gaming demon due to it sole reliance Intel’s flaccid integrated GPU.