This article is more than 1 year old
Mobile internet devices to outnumber humans this year
Skynet’s plans proceeding well
The number of mobile devices will outstrip the global population in 2012, according to Cisco’s latest Global Mobile Data Traffic Forecast.
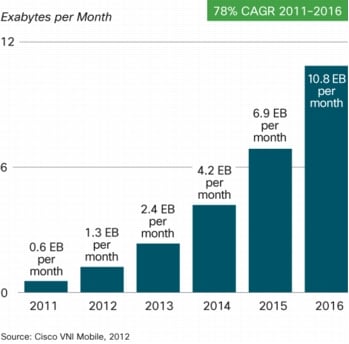
The company predicts that the number of mobile devices, including those for purely machine-to-machine contact, will pass the human population this year – and there will be over 10 billion by 2016. In terms of mobile data, Cisco is predicting a compound annual growth rate (CAGR) of 78 per cent for the next five years, so that by 2016 the world’s mobile networks will carry 10 exabytes of data each month.
Data use continues to soar
Not surprisingly, the higher-end the device and the faster the connection, the more data is used. At the moment, the biggest mobile data consumers are laptops, and Cisco estimates this will continue until they are overtaken by smartphones in 2014. The average laptop user generates 498 times the mobile data of a standard feature-phone user, ahead of tablet users (x120) and smartphones (x35.)
The study predicts that by 2016, 4G (in whatever form) will account for just 6 per cent of mobile connections, but will be responsible for 36 per cent of the traffic. The average bit rate last year was 189Kbps, but this will rise to nearly 3Mbps by 2016.
The bulk of this traffic is going to be video. Cisco expects mobile data to grow 25 times by 2016, and by that time two-thirds of the traffic will be video. A lot of this will be viewed on tablets, with iPads and their ilk expected to account for the equivalent of the current worldwide mobile data use by 2016.
The biggest geographical growth area in mobile data isn’t Asia, oddly enough. Africa and the Middle East will have a CAGR of over 100 per cent, with Asia growing 84 per cent. China is growing fast, however – it currently accounts for less than 5 per cent of global mobile data, but that will rise to 10 per cent by 2016. ®
