Can I get a rewind?
As far as the story goes, FF XIII-2 is a true sequel to its predecessor, beginning just a short time after events of the previous game and once more set across the worlds of Pulse and Cocoon.

Just as things were looking up...
To be precise, it begins within a beachside village, as a mysterious spiky-haired, dual-sword wielding chap from the future, one Noel Kreiss, appears as if from nowhere. A good job too, given Serah and the rest of her fellow villagers have come under sudden and violent attack.
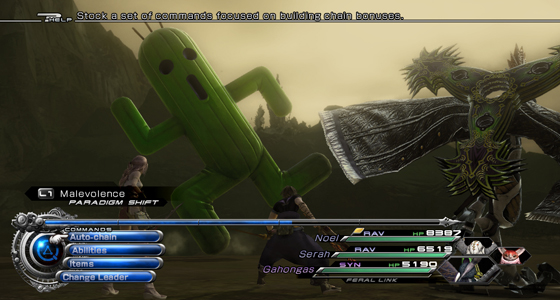
It’s the first time you’ll get to experience the games ‘Paradigm Shift’ combat, a system much debated when it debuted in FF XIII and a system which, once again, removes the need for any genuine user-participation.

Lights, paradigm, action
That’s not to say you’ll do nothing, there’s still the action button to hammer as you hit the auto attack choice – the AI nearly always picking attacks most effective against your current foe.
Paradigm shifting itself is perhaps where the player has most impact – much as a football coach might change tactics mid match – as you’re able to swap character roles on the fly. For instance, turning one of your charges into a medic and the other into a sentinel (a defensive role) when the going gets tough.
You'll peyote for your crimes!
For those who delight in this managerial type role, it’s all well and good, but as a veteran of Final Fantasy games past, it all feels rather removed and impersonal – a complaint made of its predecessor. In a failed attempt to paper over the cracks, larger foes can trigger quick time events – the successful completion of which causes damage to said foe, but it’s really nothing particularly game changing.
