This article is more than 1 year old
How can family sysadmins make a safe internet playground for kids?
The scourge of Sonic the Hedgehog abominations
Control via Choc box
That's great for simple site blocking, and takes out a lot of accidental clicks that might otherwise cause problems, but realistically children are going to spend most of their time on YouTube and Google, so one becomes dependent on what the Chocolate Factory is prepared to offer in the way of content control.
The answer isn't a lot. Google's safe search (which also exists for YouTube) can only be locked on by the account holder, and Google brooks no concept of a family account. One might imagine that a corporate account would work: Google lets one set up such a thing for free, but while employee accounts can be prevented from creating YouTube channels, or accessing YouTube at all, they can't be restricted in the kind of content which can be accessed.
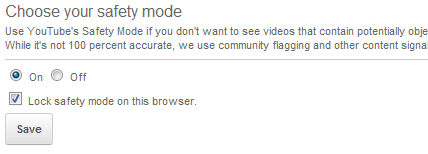
Locking by the account-holder is fine if one is lending a laptop or tablet to a child, just switch on safe search and lock it on, thereafter it can't be turned off without entering the account holder's password. But that falls down if one is trying to deal with multiple devices, and use one's own computer at the same time, so another approach is needed.
For Google the same thing is in the top right corner, under Search Settings
One solution, admittedly a bodge job, is to create GMail accounts for the children to use themselves, but don't give them the requisite passwords. Log the device's browser onto Google and switch on safe search, do the same thing to YouTube and one should be safe to leave the child to click through links and videos with limited damage - though it's worth remembering that YouTube content in particular is only peer reviewed. Dodgy content will only be restricted after someone has reported it as such.
None of this is foolproof, and none of it substitutes for attentive parenting, but desirable as it might be one can't spend every moment watching the children watching the internet. Just as one tries to watch TV with the kids, there's a limit to how much Samsam one can put up with and to the children YouTube is nothing more (or less) than a TV channel that never ends.
There's also an argument which says children should be given some freedom to explore on their own, virtually as well as physically. The giggles on hearing kids discover lolcats for the very first time are as precious as any parental memory.
But trying to provide freedom while at the same time preventing them being exposed to the worst of the internet is tough, so chip in below with suggestions or advice - we only get one shot at getting this right. If we get some good tips from you lot (and frankly, who better?) we'll compile them and come back with a Reg guide on the subject. ®
