This article is more than 1 year old
Netgear ReadyNas Duo v2 network storage
ARM twist tactics
Community centre
All of these configuration choices are gracefully handled by the RAIDar software that’s available in Windows, Mac and Linux flavours. RAIDar locates and helps you configure any ReadyNas device on your network. Although the setup itself is relatively easy, I had to leave it overnight to complete a full restore to factory defaults and configure a new X-RAID2 array.
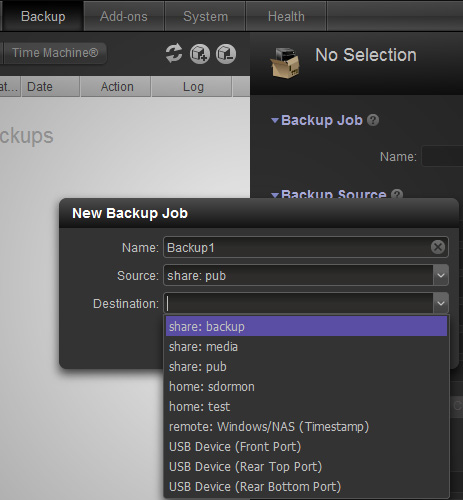
Backup location
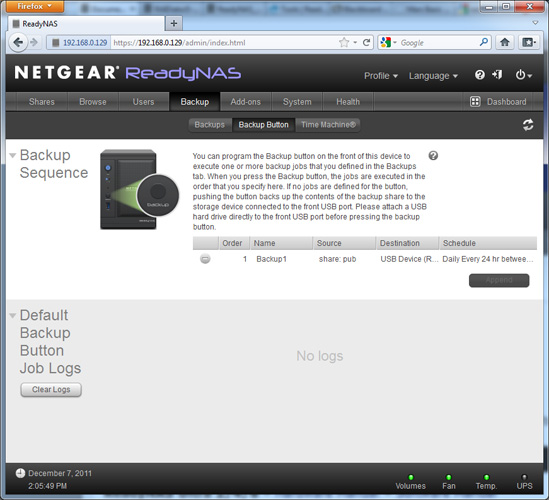
Once you’re up and running the FrontView web interface takes over for the rest of your ReadyNas journey. This latest version is considerably smarter in appearance than that featured on earlier SPARC and x86 models. It’s also considerably faster, with the ARM chip proving very snappy and responsive and it's a quiet box too, thankfully. Browse around FrontView and you’ll find all the usual compliment of Nas features such as user configuration, filesharing, DLNA media streaming, personal web hosting and more.
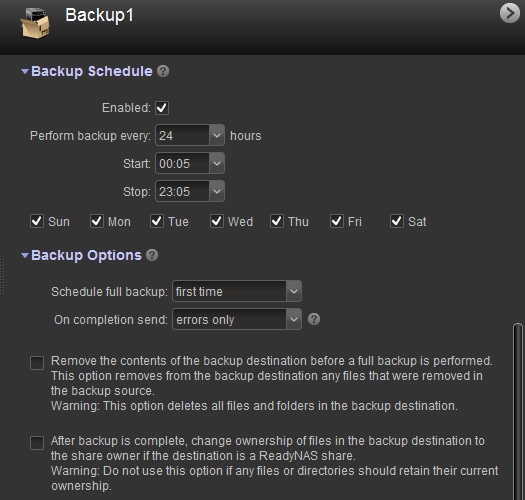
Backup schedule
Previous models have notched up quite an extensive library of third party software add-ons courtesy of the ReadyNas developer community. What’s on offer has taken somewhat humble hardware to levels of functionality Netgear likely never imagined. I was looking forward to all of this and more with the Duo v2, only to be disappointed that the introduction of the new ARM CPU has rendered nearly all of these software add-ons incompatible.
At time of writing there were just a handful of ARM-compatible add-ons: ReadyNas Photos II, ReadyNas Remote and Transmission (the popular BitTorrent client) as well as PHPMyAdmin (browser-based SQL manager) and Sabnzbd a binary newsreader.