This article is more than 1 year old
Implementing, serving, and using cloud storage
The SNIA's great introduction to cloud storage
Cloud Storage
A cloud represents a “fuzzy” container for data, and the user doesn’t really care how the cloud provider implements, operates, or manages the cloud. A client, through the medium of a network, makes requests to the cloud storage to securely store and subsequently retrieve data at an agreed level of service.
Regardless of the data type managed, whether it be files, objects or even traditional SAN LUNs, cloud storage is a pool of resources that are provided in small increments with the appearance of infinite capacity. In other words, cloud storage is virtualised storage on demand and is more formally called 'Data Storage as a Service' (DaaS). DaaS is defined as “Delivery over a network of appropriately configured virtual storage and related data services, based on a request for a given service level.”
As vendors and suppliers of cloud services have delivered early implementations to users, they have tended to supply a multitude of interfaces that have been re-purposed for DaaS, such as block-based access via iSCSI; POSIX interfaces (NFS, CIFS, and WebDAV); object-based CRUD (Create, Read, Update, Delete) interfaces over HTTP; and a plethora of other proprietary interfaces for database or table access
CDMI: The Complete Picture
Clients can adapt their existing, proprietary interface, while still allowing access via CDMI or standards-based interfaces, such as POSIX, XAM and so on. They can adapt their interface by:
- Abstracting the data and storage services into data storage cloud containers
- Providing a consistent and uniform interface to gain access through CDMI
The CDMI defines the functional interface that applications can use to create, retrieve, update, and delete data elements from the cloud. As part of this interface, the client can discover the capabilities of the cloud storage offering and use this interface to manage containers and the data that is placed in them. In addition, metadata can be set on containers and their contained data elements through this interface.
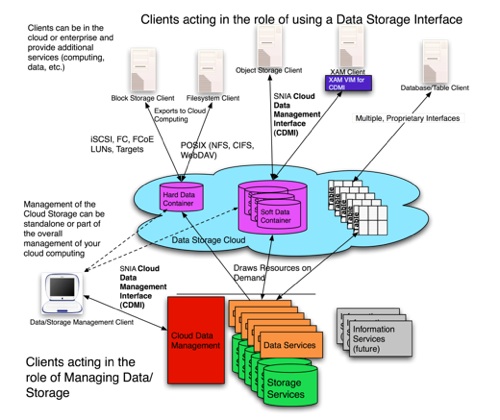
SNIA cloud storage schematic
The same interface is also used by administrative and management applications to manage containers, accounts, security access, and monitoring/billing information, even for storage that is accessible by other protocols. The capabilities of the underlying storage and data services are exposed so that clients can understand the full capabilities of the storage being used.
