This article is more than 1 year old
German boffins BREAK LAWS OF THERMODYNAMICS!
Kelvin joins Einstein in has-been corner?
As you probably know, heat is one of the enemies of electronics, and heat management is a major design constraint of microelectronics. Now, a German research group has demonstrated using waste heat to get electricity.
No, we’re not really talking about perpetual motion here. What the researchers have observed is that in magnetic tunnel structures, changes in temperature produce a voltage across the structure.
We already use magnetic tunneling in hard drive and MRAM (magnetoresistive) technologies. The PTB Braunschweig say the thermoelectric effect they have observed could be used to monitor and control the thermoelectric voltages in highly integrated circuits.
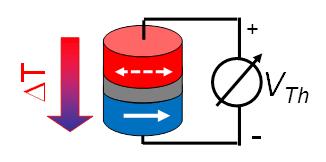
The temperature difference across a magnetic tunnel
can create electricity, German researchers say. Source: PTB Braunschweig.
The magnetic tunnel consists of two magnetic layers separated by a 1nm insulator. When used in something like a disk drive head, magnetization is used to control the current flowing across the structures. When the magnetic poles are aligned, current flows freely; when opposed, resistance is much greater.
What the PTB researchers have noted is that the magnetization of the layers also impacts how the thermal current flows. The thermal resistance of the structure, like the electrical resistance, is greater when the poles are opposed.
If the structure is heated unevenly, it generates a thermoelectric voltage across the structure, effectively turning waste heat in a system into a small, but usable, source of electricity for other components. ®
