This article is more than 1 year old
Android mobes sneak into enterprise pockets
While the world was waiting for the iPhone 5
The last three months provided an unprecedented opportunity for Android devices to get themselves integrated into enterprise systems while the world waited for the iPhone 5, according to the latest figures from Good Technology.
Good tracks devices that have been registered with its push email infrastructure, generally employees' own devices that have been provisioned on the company network, and reports that while the iPad has topped out and the iPhone is slowing down, in terms of registrations, Android devices have been quick to fill the void.
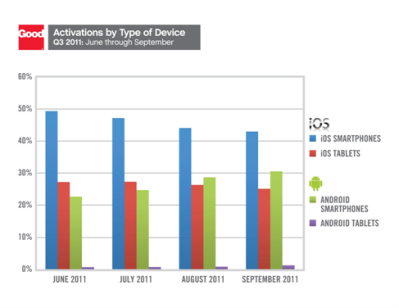
Not that the void will last long, according to Good; the analysts put the rise in Android registrations firmly down to the fact that everyone was waiting for the much-rumoured iPhone 5. Good VP Andy Jacques assured us that the company fully expects to see a surge in registrations as those four million iPhone 4S handsets get brought into the office.
Having said that, it's worth noting that Good saw a lot of Android growth in 4G handsets: the Sprint EVO 4G and HTC Thunderbolt both offer headline speeds with which the iPhone 4S can't compete.
But when it comes to tablets there's nothing holding Apple back or offering decent competition to the iPad's dominance. Android tablets make up only 1 or 2 per cent of the total, described by Good as little more than a rounding error.
Good has been having a hard time keeping a straight face following the convulsions afflicting RIM's infrastructure. The company gets no figures for RIM devices but reckons the writing was on the wall for the BlackBerry maker anyway as companies increasingly expect their staff to provide their own mobile-computing technology, and thus need a messaging platform that works across device platforms.
We can't help noting that such bring-your-own-tech policies never seem to extend to the upper echelons, but that's not Good's fault, and if employees want the latest iGadget then companies would be foolish not to let them pay for it. ®
