This article is more than 1 year old
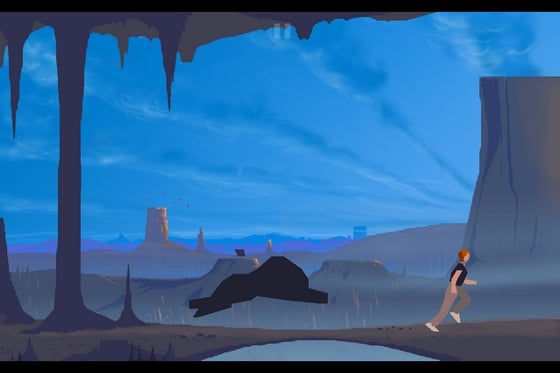
Another World 20th Anniversary Edition
Poly gone?
iGamer It's one of gaming's longest enduring and most profound existential questions. Twenty years and as many platforms later, Another World - aka Out of this World in the US -remains as enigmatic as ever, surviving even creator Eric Chahi's own fascinating personal deconstruction of his work at this year's Game Developers Conference.
With only minor graphical improvements and some niggling control issues, the 20th Anniversary iOS edition might not rank as the definitive version – that accolade still rests with the 15th Anniversary PC edition.
Wot no polygon textures?
But thanks to its distinctive visuals, idiosyncratic gameplay and hauntingly evocative fiction, Another World feels as visionary today on iPhone or iPad as it did on the Amiga way back in 1991.
Even when considered alongside the advancements of the past 20 years, the platform puzzler still ranks up there as one of gaming's most innovative titles. Its ability to charm and infuriate in equal measure is as potent in its first playthrough as in its one hundredth.

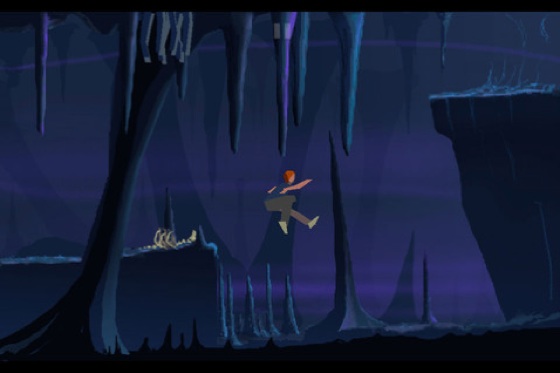
AW's animation was painstakingly rotoscoped
Thanks largely to its reticence, the story feels timeless too. You play Lester, the flame-haired, Ferrari-driving physicist teleported to a hostile alien world when his particle accelerator is hit by lightning.
To help you survive, you must rely on your wits, a blaster and occasional help from a friendly alien called Buddy. But with no further exposition or interface to guide you, your truest friend here is gaming's most conventional foe: death.
The fuzziness of touch control doesn't sit well with AW's pixel-precise death detection
Like its spiritual successors Limbo and Demon's Souls, Another World reveals itself through failure. Twitch platforming is the only skill required to survive its pitfalls, trial and error the only logic to solve its esoteric puzzles.
