This article is more than 1 year old
Which actor should play Steve in upcoming biopic?
Insanely great casting needed
After this week's announcement that the late Steve Jobs will be remembered through a Hollywood biopic, the obvious question facing Sony Pictures is… which actor gets the nod for the lead role?
The film rights to Walter Isaacson's biography, due to be published later this month, was snapped up by Sony Pictures for a healthy sum, with Source Code's Mark Gordon earmarked to produce the movie version.
To cash in on the current hype though, the studio will have to act fast. But who is the right man to step into Steve's shoes?
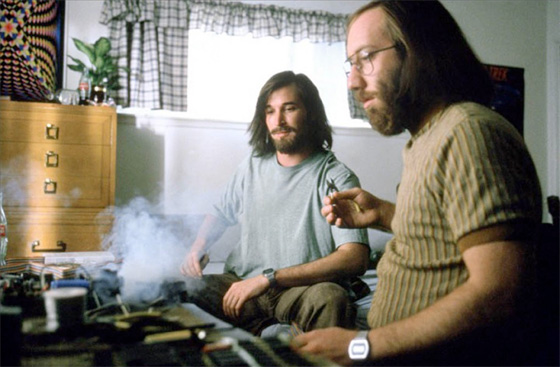
Noah Wyle as Jobs and Joey Slotnik as Woz in Pirates of Silicon Valley
Noah Wyle did a very good Job(s) in the 1999 TV film Pirates of Silicon Valley, but a fresh face is likely here. Perhaps even two actors are needed: one for the young bearded hippie who created Apple and another for the bloke who oversaw the iPod generation.
Finding lookalikes in the acting world is much harder than it seems, though. Aston Kutcher, Stanley Tucci... Christopher Eccleston? Let us know who you would choose. ®
