This article is more than 1 year old
Google loses battle for goggle.com
Typosquatter's rights upheld – for now
Google has lost its cybersquatting fight with typo-snaffle site goggle.com, enabling its owner to carry on enticing clumsy typists into signing up for pricey text messaging services.
The company's complaint against the domain name's current registrant, Barbados-based David Csumrik, was dismissed on procedural grounds yesterday by a three-person National Arbitration Forum panel in the US.
Right now, Goggle.com's website asks visitors a short series of questions before attempting to persuade them to sign up for a £3-per-text quiz competition, offering the latest Apple products as prizes.
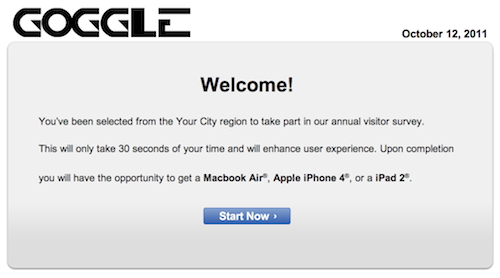
This isn't the search engine you were looking for
This is the preferred money-making scheme today for typo-targeting domains of high-traffic websites. Twitter filed a similar complaint over the domain name twiter.com in June.
Google attempted to slay goggle.com by wielding the Uniform Dispute Resolution Policy, which was designed to give trademark owners a way to take domains from cybersquatters without resorting to expensive litigation.
While goggle.com appears primarily to take advantage of butterfingered web searchers, the NAF panel declined to consider the UDRP's standard tests of "confusing similarity" or "bad faith registration".
Csumrik, in his response to Google's complaint, showed paperwork claiming that Google and the disputed domain's previous owner, Knowledge Associates, had legally agreed to "co-exist".
Those rights transferred to him when he bought the domain, he claimed.
This was enough to convince the NAF panel that the dispute was "outside the scope" of the narrowly focused UDRP, which does not deal with contractual or business disputes.
"Does the Co-existence Agreement apply to the disputed domain names? Does Respondent stand in the shoes of the original registrant? Does the consent of Complainant extend in time to the current actions of Respondent and in person to the Respondent? Has the Respondent complied with the obligations of the original registrant?" the panel asked. "These are factual and legal issues that go far beyond the scope of the Policy."
While the decision is good news for goggle.com's owner, it may be too early to break out the champagne – if Google is determined to get hold of the domain, it may now resort to expensive court action. ®
