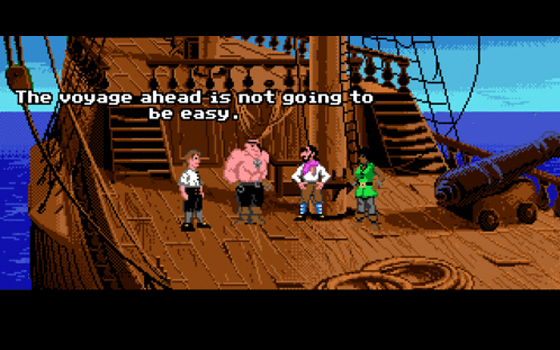
Antique Code Show The Secret of Monkey Island ignites the urge to buckle swashes in everyone and 20 years on from its debut everyone I know still loves this game.
She goes sixty miles to the galleon
Especially my friend Pippa, who manages to constantly find parallels between our pop punk adventures and Guybrush Threepwood's buccaneering quests. Maybe this has something to do with the game's awesome soundtrack - a tip of the (tricorn) hat goes to composer Michael Land.

'Cockatoo?'
'Why, how many have you nice young man, you?'
To me, Monkey Island represents more than a game I enjoyed back in the day. It’s the first game that really sucked me in. The first game that transported me to another realm, that took me on an adventure that innumerable other games in the same genre would try in vain to imitate, but never quite equal.

OK, but you'll need to change your name. How about 'Seaman Staines'?
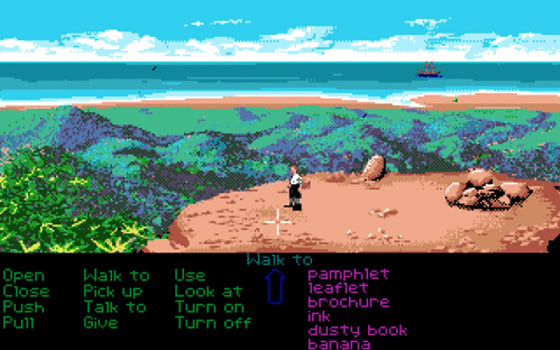
The best thing about Monkey Island is its combination of wonderfully droll pirate storyline and gratifyingly Machiavellian puzzles. It was the fifth game to use the SCUMM (Script Creation Utility for Maniac Mansion) gaming interface: choose a verb and an object to couple it with, and the game would provide a response.
Is that The Black Pig out there?
I play aspiring pirate Guybrush Threepwood, a gullible young dude with a thirst for adventure and a complete lack of awareness of what lies ahead. There’s no looking back as I quest to fulfill my misbegotten destiny and solve the strange secret that lies in at the heart of Mêlée Island, the pirate-infested hub of Monkey Island.

Isn't this street a little clean for the 18th Century?
At a local tavern, a trio of pirate leaders gives me three trials to complete in order to be considered a proper pirate. The challenges test my pirating abilities in sword fighting - peppered with insults and witty comebacks, scripted by sci-fi scribe Orson Scott Card - looting and treasure hunting.
