This article is more than 1 year old
IEEE task force massages 100GE for backplanes
25Gb/sec signaling for blade servers
The IEEE standards body has set up a task force of industry vendors to start work on the four-lane, 25Gb/sec signaling that will be required for future 100 Gigabit Ethernet.
The group will also thrash out the specs that will allow 100GE to be used in server and network equipment backplanes and over short-haul copper wires.
Specifically, the IEEE has approved an amendment to the 802.3 standard for 100GE networking called P802.3bj, which will enhance the physical layer in 100GE devices and complement the existing work that has been done in the 802.3ba-2010 standard, which relates to the data link layer of the network stack and which was approved as a standard for 40Gb/sec and 100Gb/sec Ethernet devices last June.
The task force working on the P802.3bj extensions for 100GE is focused on the use of Ethernet as a backplane interconnect inside of blade servers and across racks in 1 meter or shorter hops and in copper cables that are 5 meters or shorter for inter-rack and cross-rack connections.
"From the challenges of ever-increasing front-panel capacities to continuing advances in processors, high-performance computing, and server virtualization technologies, the ability of systems to meet spiraling bandwidth demands remains challenging," said John D'Ambrosia, chair of the P802.3bj task force. "By expanding on the solid foundational standards work already completed, IEEE P802.3bj will provide better options for system designers to minimize or eliminate the bandwidth bottlenecks facing end-users."
D'Ambrosia is chief Ethernet evangelist in the office of the CTO at Force10 Networks (now part of server maker Dell) as well as chairman of the Ethernet Alliance, a vendor-driven trade group to help steer Ethernet technology.
The long road to the 100GE backplane standard
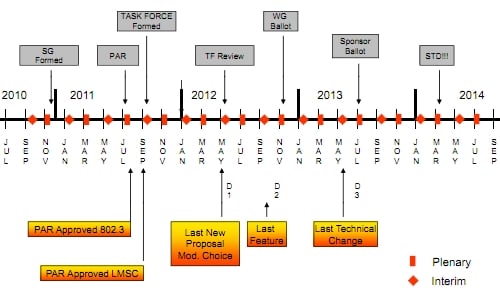
The 100GE backplane and copper cable standard announced today expects to have a review put together by next May, with the last features added in September 2012, the last technical changes due around May 2013, and a standard ready by March 2014. ®
