This article is more than 1 year old
'Anon member' claims credit for WikiLeaks takedown
Friend turns foe
A Twitter user who claims affiliation to the infamous Anonymous hacktivist collective has claimed responsibility for launching denial of service attacks that floored WikiLeaks on Tuesday night.
The attack against the whistle-blowing site occurred at the same time as less high-profile assaults against Pastebin and 4Chan, the anarchic image board and birthplace of Anonymous.
The assaults were reportedly field trials for a new JavaScript-based DDoS tool, dubbed RefRef, designed to exploit SQL server flaws on targeted websites. RefRef is the successor to the notorious LOIC attack tool, which discloses users' IP address by default, as many arrested hacktivists now know only too well.
Anonymous began with attacks against the Church of Scientology three years ago, but only gained mainstream fame when it launched denial of service attacks in support of WikiLeaks and against financial service firms that shut down accounts maintained by the whistle-blowing websites.
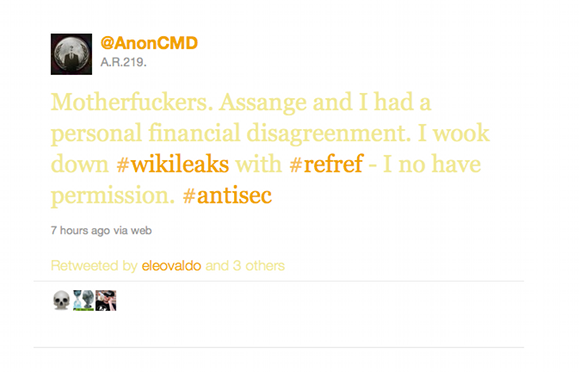
A Twitter account (@AnonCMD) linked to an Anonymous activist refers to a "personal vendetta against WikiLeaks" adding that "we are sorry we took you down. We are even".
An update to the account indicates that the dispute is over money supposedly owed by Julian Assange. ®
