This article is more than 1 year old
Nokia's Ovi wunderkind is off ... to Nokia-backed Vision+
Ojanperä brings unbeatable track record - of disasters
One of Nokia's high flyers is leaving the company – but will still be spending Nokia's money. Tero Ojanperä, an executive vice president, member of the core Leadership Team (and, don't forget, UN Young Global Leader) will head up a Nokia-backed investment fund called Vision+.
The new investment fund "seeks to help communities turn creativity and innovation into products" – but this was a challenge at which Ojanperä, a brilliant radio engineer, was conspicuously unsuccessful. Ojanperä's later career may embody the Peter Principle in action.
Ojanperä oversaw the push into services under the now abandoned Ovi umbrella brand, and his pet brainchild was Comes With Music – another global failure. He hired Dave Stewart as a "change agent", and Stewart in turn discovered Cindy Gomez, a nubile singer who, like Nokia's products, had the ability to be bland in several languages.
Lately, Ojanperä was responsible for expensive vanity projects such as the creepy interactive multi-million pound "game" designed to raise "global consciousness". It didn't seem to make much impression on local consciousness however, and over several weeks drew fewer participants than hired staff.
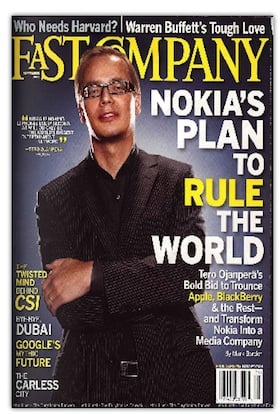
"Transform Nokia into a Media Company"
Getting in new blood to drive services and media partnerships may be one of the few brights spots of the Microsoft deal, we mused back in February.
The Finnish giant wanted to create ground-breaking media partnerships, and for this it needed a Steve Jobs, a media schmoozer in the Hollywood tradition. Instead it appointed a space cadet. As late as last year Ojanperä was referring to Apple dismissively as "that fruit company".
The habit of hiring eccentric labs people into jobs for which they're completely inappropriate hopefully ends here. But then Nokia recently replaced its CTO Rich Green with a researcher who had studied the "dynamics of karma".
Where do they find 'em? ®
