This article is more than 1 year old
David May, parallel processing pioneer
We salute the architect of the Transputer
Shrinking the minicomputer
Tiny computers were already available to May. Intel, founded in the late 1960s by Robert Noyce and Gordon Moore as a memory manufacturer, had already introduced the 8-bit 8008, the chip credited as the seed for the PC revolution.
But the processor May eventually chose came from Texas Instruments. "The TM9900 was a PDP-11-like machine on a chip," he says. "It had fast serial interfaces, so I was sticking these things on boards, each with their own memory, and then networking them together for message-passing."
The system needed a programming language, so May wrote something he called EPL - Experimental Programming Language. At Cambridge he'd been taught compiler writing by Martin Richards, whose own BCPL programming language laid down the foundations for what eventually became C. BCPL was the language that drove the Warwick departmental minicomputer, the Modular One, built by a company founded by British engineer and entrepreneur Iann Barron.
"The BCPL compiler was faulty," says May, "because the port to the Modular One was never finished." Fixing BCPL was May's nursery slope to developing EPL.
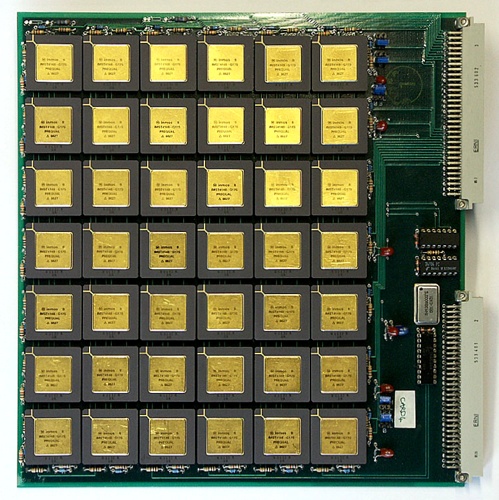
One board - the B000 - 42 Transputers
From Parallel Theory to Practice
But EPL was very different. BCPL instructed a single processor to do one thing, and then the next thing, and then the next. EPL sent out its instructions to a hive of processors, each with its own memory. This made them effectively autonomous computers, and EPL's job was to distribute tasks among them and co-ordinate the results.
The far-from-trivial logic behind this kind of parallel computing had been formulated in the mid-1970s in a paper by Tony, now Sir Charles Antony Richard, Hoare. Already famous for Quicksort, the widely used sorting algorithm, Hoare had devised a theoretical language, CSP (Communicating Sequential Processes) that might enable parallel computing. It was this logic that May was now trying to implement in the real world.
May wasn't alone in his quest for workable parallelism. "In 1975, 76 there were three groups in the UK," says May. "Myself and a colleague, a couple of guys in Edinburgh, and George Coulouris and his group at Queen Mary College. We'd all, in one way or another, made proposals to the then Science Research Council (SRC) to do research on distributed computing when nobody knew what it was."

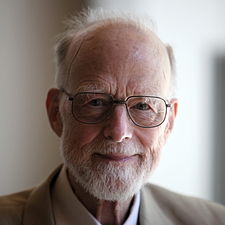
Dramatis Personnae: Iann Barron (left) and Tony Hoare
Source: Mark Jones/Inmos.com (IB) and Wikipedia (TH)
Nobody in the Labour government knew either. There was no Minister for Information Technology, although there had been a vociferous advocate for one for several years: Modular One maker Iann Barron. And it was to Barron that the SRC turned for advice.
