This article is more than 1 year old
David May, parallel processing pioneer
We salute the architect of the Transputer
Footnote or stepping stone?
When Inmos was sold to Thorn EMI under the privatising Thatcher government in the mid-80s, and later to SGS Thomson, Transputer development continued, but was eventually abandoned.
The end of an era? It's not so easy to kill the Hydra-headed Transputer. The site of the original Inmos design centre in Bristol is now owned by STMicroelectronics. It is ablaze with engineering talent nurtured under Inmos.
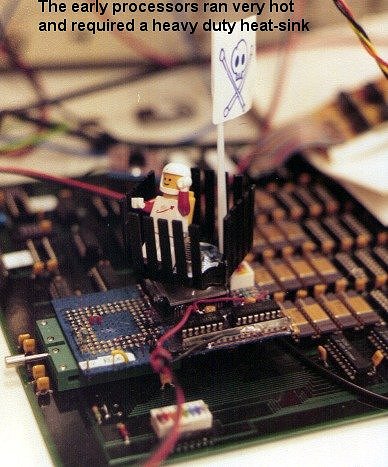
Source: Ram Meenakshisundaram/Inmos.com
"They're developing products that are turning over more than a billion dollars a year," says May. "And have been for the last decade. It's the biggest Silicon Valley in Europe in terms of design capability. It's all there because of this huge expertise in processor technology."
Other companies like Infineon, Element 14 and Icera have mushroomed from the same Bristol talent base, as has May's own university spin-off, XMOS, that perpetuates the Transputer idea in low-cost microcontrollers.
So Inmos paid off in UK job creation. But in these days of ever faster Intel-style processors, who remembers the technology?
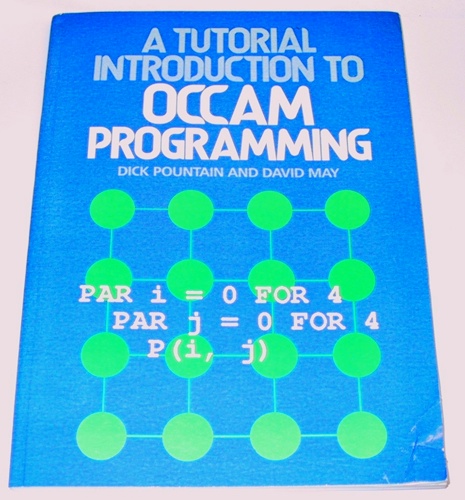
Source: PCPuter.com
Roger Shepherd was one of graduates who worked with May in the Inmos days. Now director of processor design at STmicroelectronics, he sees the ideas around the Transputer coming back into relevance. "Most PCs today have two or four cores," he says. "How to program for multicore systems is one of today's key challenges. People are now asking the same sorts of questions we were trying to answer at Inmos 30 years ago. They are trying to solve real problems that Occam overcame."
Iann Barron, now in his mid-seventies, looks back on Inmos as a venture deferred rather than defeated. He likens the Transputer to Babbage's mechanical computing engines, devised in the 19th Century, their significance not appreciated for more than 50 years after his death. "People will eventually see what we were talking about, and they'll say, 'yes, well, they did it'." ®
