This article is more than 1 year old
iPad accessorizer gets into Bernie Madoff's pants
Own a bit of butt-hugging history
Wealth and villainy are notorious aphrodisiacs, and a New York company is making it possible for you to get into the pants of one of the 21st century's highest-flying criminals.
Well, not you, exactly – your iPad.
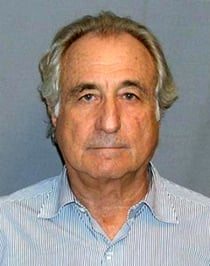
The financial felon with the ironic last name
Fashonista iPad casemaker Frederick James is offering a pair of iPad cases made from trousers formerly owned by Bernie Madoff, the swindler who bilked billions from institutions and individuals alike in the largest Ponzi scheme in history.
Frederick James specializes in cases made from what they call "rescued fabric" – and they rescued Madoff's khakis and chinos from a US marshals auction held last November to dispose of the felon's worldly goods.
How Frederick James passed up the temptation to bag "18 pairs of men's Belgian shoes, Mr. Casual style, size 9W", we'll never know. Surely they could have been transformed into foot-fetishist iPhone cases.
The iPad maker transformed those rescued trousers into a collection it calls The Bernie Madoff: one case made from Ralph Lauren Polo Chino Blue Pants, and another from Mason's Off-White Khaki Pants.

The iPad case made from Madoff's chinos
Your brush with the pantaloons of pleonexian power, however, won't come cheap: the slipcases run $350 each, even though "The Frederick James iPad covers are NOT intended to be protective if you should drop your iPad while carrying it AT ALL."
Should Madoff's slacks not float your boat, Frederick James has other "rescued fabric" lines from which you can choose: The Lodge, The Island, The Jungle, The Office, and Food and Fun. And at $60 to $95, they're far more affordable.
It's unlikely that federal inmate Bernard Madoff – aka #61727-054 – will be purchasing any of Frederick James' iPad cases anytime soon. He now resides in the medium-security unit of the Butner Federal Corrections Complex in North Carolina. ®
