This article is more than 1 year old
Mackie Onyx Blackjack USB audio interface
Solid sender
Soft options
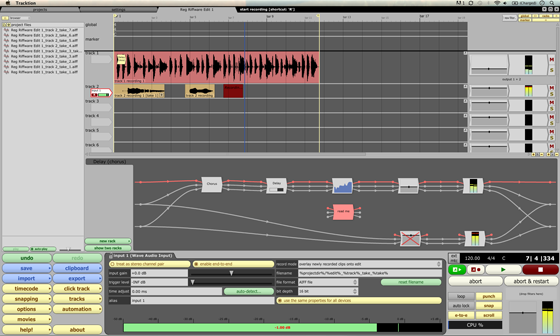
The Onyx Blackjack also comes with Tracktion 3 recording software for Mac and PC. Included in the box is a serial number for the app that you can download after registering. Tracktion is rather odd looking and initially gives the impression of being some kind of Java project, especially as it could take some time thinking about things.
Admittedly, I didn’t get off to a good start with Tracktion 3 as I’d previously set the Onyx Blackjack to 44.1kHz in the Audio MIDI Setup utility for use with iTunes and tests with Steinberg's Cubase Elements. Alas, I couldn’t get the Onyx input to work until I changed it back to 48kHz. It seems that Tracktion 3 likes to deal with any sample rate changes personally.
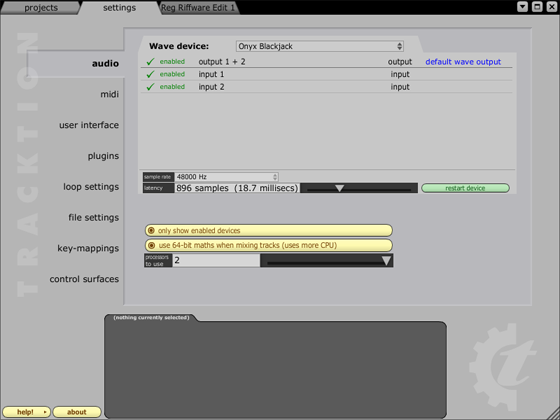
Tracktion settings menu
The app is certainly different, with project window shrinking to 800 x 600 to hand from a single click to make room for other apps or to use on a netbook. You can muddle through, but some basic tasks such as normalisation of recordings needed a few hoops to jump through (Loop edit > Loop info > Basic audio File Operations) to apply the changes. If there was a shortcut, it wasn’t obvious.
In fact, there’s quite a lot that isn’t obvious with Tracktion 3 as it does offer a rather different way of working, but it seems that perseverance pays dividends. The effects racks that can be strung together from basic Tracktion components are a bit of a diversion as there as some rather good Mackie VST effects on-board too. MIDI is supported and can trigger Tracktion 3’s on-board sampler.

VST effects on-board too
Indeed, if you didn’t take some time getting familiar with Tracktion 3, you might easily dismiss it as being basic, but it’s worth checking out the impressive demo songs that really show off its depth and capabilities.