This article is more than 1 year old
Obama drops Twitter bombs on debt-ceiling foes
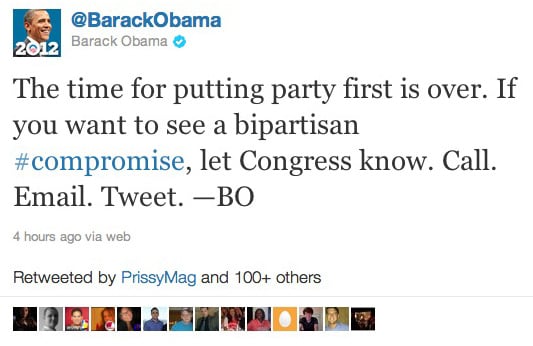
'Call. Email. Tweet. —BO'
The US debt-ceiling legislative dogfight ratcheted up a notch on Friday morning when President Obama's campaign staff launched a Twitter-bombing run on US legislators.
Shortly after Obama made a short statement in which he urged Americans to "make a phone call, send an email, tweet; keep the pressure on Washington," @BarackObama, an account run by the #Obama2012 campaign staff, began to tweet the Twitter handles of Republican senators and representatives, asking the account's 9,405,391 followers to tell those targets to accept a "bipartisan compromise".
We're decades away from the mailbag-dumping scene in Mr. Smith Goes to Washington
Obama's staff appear to be walking a fine line between the healthy encouragement of citizen participation and outright spam-mongering. What's more, the Twitter bombing may backfire on the campaign if on-the-fence GOPers move to the right in angry response to the deluge of unwanted missives.
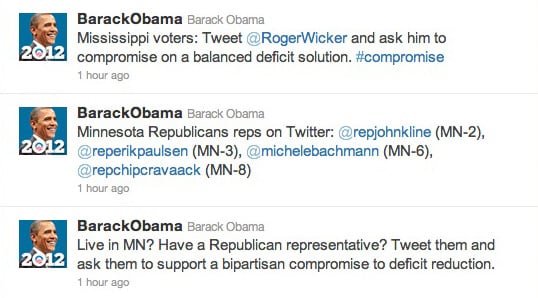
We have serious doubts that a tweet to @michelebachmann will do much good
That said, we're witnessing yet another example of how Biz Stone, Evan Williams, and their crew have changed political activism, from the Arab Spring to the long, hot, excruiciatingly infuriating summer of Washington warfare. ®
