This article is more than 1 year old
Marathon for iPad
'Frog blast the vent core!'
iGamer To hear PC gamers talk about how first-person shooters don't work on consoles because the machines don't have mice, you'd think that's how it always was.
Not a bit of it. A lot of us playing in the early to mid-1990s on the first FPS games made do with just two handfuls of keys.

Marathon: back from the early 1990s in all its eight-bit graphics glory
I say this because the proof that FPSes are not at all dependent on a keyboard-and-mouse combo is the number of such games running on tablets; and if they can be played successfully there, they can be played on anything, console, PC or whatever.
The latest to do so is Marathon - doubly relevant here because, although little known now, it was one of the pioneers of the FPS genre. Its developer, Bungie, went on to create a title you may have heard of: Halo.

3D environments... 2D sprites
Marathon arrived in 1994 about six months after Doom hit the PC, and its lack of fame wasn't so much because it was under the shadow of its meatier, more visceral rival, but was rather a result of being released on the Mac.
Doom's real success lay in its multi-player mode. Marathon had that too, but it was really a single-player game, and one that lifted the genre right out of the 'kill monsters, find key, open door' gameplay with a developing storyline that was a worthy piece of sci-fi in its own right.

Pfhor whom the bell tolls
You start off fighting alien slavers who are out to plunder your colony ship - the eponymous Marathon - of its human crew, the born on board BOBs. But soon you discover, by tapping into the ship's many display terminals - no cut-scenes in those days - that they've been called in by one of the ship's computer, and gone "rampant" - become self-aware.
The cliché is confounded when it turns out said mech, Durandal, isn't bonkers but has been in communication with one of the slavers' pawn races, the fnarr-ly named S'pht, and has set the whole thing up to bring them there because they can free Durandal from his integrated circuit bondage.
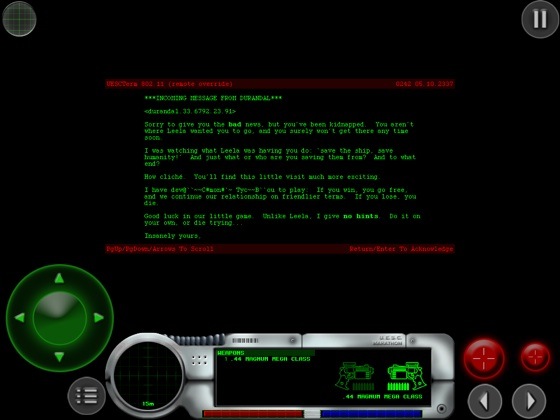
Terminal case: the story unfolds through computer screens
In return, the S'pht get freed from Pfhor subservience, and you, a proto-Spartan cybernetic construct built out of the body of a long dead man - hence your ability to reanimate when 'killed', a phenonomenological paradox ignore by most games - prove to be Durandal's pawn to keep the Pfor off his back.
Which involves much bloodshed, dispatching Pfhor warriors, various slave races, damage Marathon defence droids and more.
