This article is more than 1 year old
Fox News tweets hacked to show Obama death stories
Foxy pranksters outfox Fox for lulz
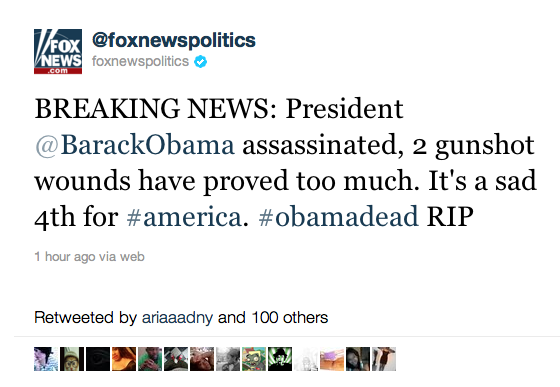
A Twitter account maintained by Fox News has been hacked to post fake "Obama assassinated" stories.
The @foxnewspolitics account was seized to post a succession of bogus updates (example below) on the false story that Obama was shot and killed while supposedly campaigning at a Ross' restaurant in Iowa.
The obviously compromised account has more than 33,000 followers. Such hacks are often an attempt to trick surfers into visiting links for more information that actually land on sites running fake anti-virus scans. No malware payload or links have yet appeared in this case, though that could easily change.
It is unclear who pulled off the attack but it bears the hallmarks of an attack carried out for bragging rights and using password-guessing, possibly by a group of LulzSec wannabes. The timing of the hack early on Monday morning (US time) coincides with US Independence Day. ®
