This article is more than 1 year old
Boffins fix dead satellite using 'dirty hack' in space
Eat that, LulzSec
Engineers and ground controllers at the European Space Agency are overjoyed to announce that they have managed to bring an unexpectedly defunct, critical science satellite orbiting the Earth back to life – by hacking it.
Forget user logins, this is real hacking
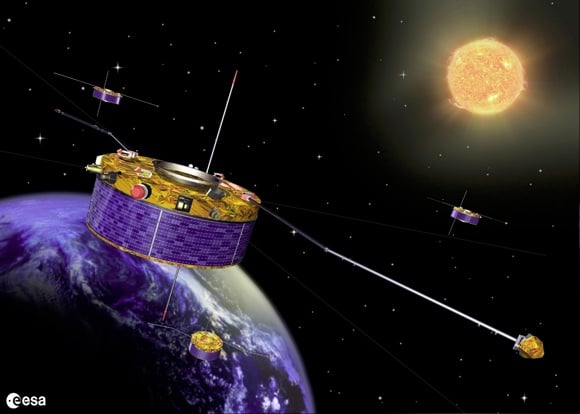
The satellite in question is known as "Samba", and is one of four sent up in 2000 to carry out specialist analysis of the solar wind. A loss of any of the quartet can be enough to invalidate the data from the others, so when Samba's vital Wave Experiment Consortium (WEC) instrument cluster went down in March, ESA controllers at Darmstadt in Germany were very upset.
"When everything goes as planned, flying a mission can be routine," says ESA's Manfred Warhaut, Head of Mission Operations. "But when unexpected trouble occurs, and there's nothing in the manuals, you really want to have an experienced and talented team on hand to solve the problem."
Warhaut and his fellow satellite experts feared that there had been a paralysing short circuit aboard the spacecraft, but managed to use a piece of dormant software in its computers to find out that in fact all five power switches on the WEC had locked closed – a condition that was considered unrecoverable according to the manual. The satellite simply was not supposed to be able to come back from that situation.
But as all hackers know, most kinds of system can be made to do things they aren't supposed to. The ESA's team managed in the end to hack Samba and get it to fire up its WEC again.
"The solution was based on a 'dirty hack' – jargon referring to any non-standard procedure – but we really had no other option," says Jürgen Volpp, Cluster operations manager.
According to an ESA statement, "Cluster has since returned to normal operation". ®
