This article is more than 1 year old
Scientists print out solar cells using inkjet tech
Sheet hot
While 3D printers spew out house keys, ladies' swimwear and even compete with Gordon Ramsay in the kitchen department, the lowly inkjet has effectively been shoved aside. There's still some life in the old boy yet, though, after scientists used one to print solar cells.
Boffins from Oregon State University (OSU) claim to have put together the world's first 'CIGS' solar device with inkjet printing.
CIGS, which stands for the copper, indium, gallium and selenium found within, is a compound also known as 'chalcopyrite' and is apparently perfectly suited for thin-film solar cells.
Using inkjet technology, the team squeezed out CIGS-based solar cells able to convert light into power with an efficiency of five per cent efficiency. That's too little to replace today's solar panels, but the scientists reckon their technique has the potential to reach an efficiency of 12 per cent. This would put it in the frame for commercially viable solar cells.
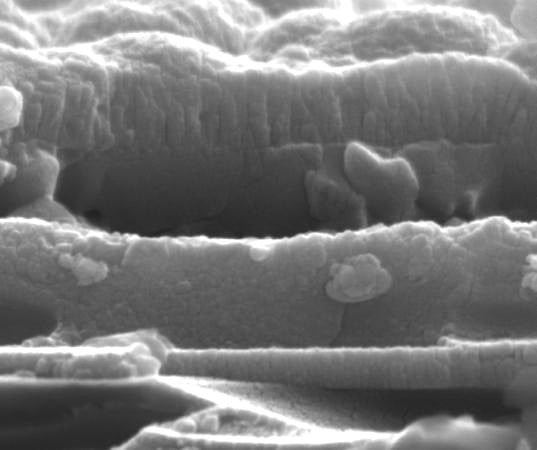
Solar cell up close
Apparently, a layer of chalcopyrite just one to two microns thick can capture the same energy as a 50 micron layer made from silicon. The inkjet technique reduces raw material waste by a staggering 90 per cent.
OSU professor Chih-hung Chang highlights the dramatic reduction in wasted resource,
"Some of the materials we want to work with for the most advanced solar cells, such as indium, are relatively expensive," he said. "If that's what you're using you can't really afford to waste it, and the inkjet approach almost eliminates the waste."
As it stands, we're unlikely to see solar ink cartridges appear at our local Rymans, but the potential is huge and if costs can be reduced enough and the process tweaked properly, scientists say it could be used to build solar panels directly into roofing materials.
The idea of printing sun-soaker cells is nothing new. 'Power Plastic' manufacturers Konarka Technologies produced solar panels in 2008 using inkjet techniques. They weren't quite the same, though. ®
