This article is more than 1 year old
Want to keep Android apps from spying on you?
WhisperCore to the rescue (some restrictions apply)
A security researcher has released an Android app that allows users to control precisely what information they share with other programs installed on their smartphones.
The latest version of WhisperCore remedies a shortcoming of the Google mobile operating system that has vexed users since its release: a design that often forces them to share their precise location or unique phone identifier with app developers even when the sensitive information has nothing to do with the service being offered.
For years, Google has failed to address complaints about this take-it-or-leave-it approach, so Moxie Marlinspike, the principal behind Whisper Systems, has taken matters into his own hands. Version 0.5 of WhisperCore offers a simple interface that provides fine-grained control over what data apps may access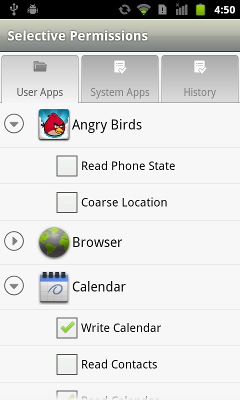 .
.
“WhisperCore's selective permissions take Android beyond all-or-nothing decisions, giving you fine-grained control over what data your apps have access to,” an announcement for the new feature said.
The application provides a list of apps installed on the handset and lets users uncheck a box next to each piece of data the apps want to access. Angry Birds, for instance, which can't be installed unless users agree to share their location, can be denied this data with the tap of a touch screen.
Other apps have attempted to do much the same thing by revoking access to those resources, causing the denied apps to crash. WhisperCore takes a different approach by supplying selected apps with randomized location coordinates or device identifiers or a contact database that's empty.
WhisperCore runs only on the Nexus S and Nexus One handsets, but getting it to work on a wider range of hardware is “definitely a priority,” Marlinspike told The Register. ®
