This article is more than 1 year old
WTF are... connected appliances?
I want my automated kitchen, and I want it now
The ‘internet fridge’ is a much-loved staple of futurologists. In some rosy and not-too-far-off future, many kitchens will have one, magically replenishing itself so that you never need run out of black pudding or milk.
When you’re low on such essentials, the fridge will automatically order new ones from the supermarket, and fresh supplies will arrive in the nick of time.
Or perhaps it’ll tell you what you can make for dinner, based on your dietary preferences and what it's containing, taking into account when things need to be eaten by.
Never again will you find a decomposed cucumber lying forgotten at the bottom of the salad drawer.
That’s the theory, at any rate. Clever appliances can help us eat better, reduce waste and make life simpler. So why aren’t our kitchens – and the rest of our homes – full of intelligent connected appliances?
'Buy some milk on your way home'
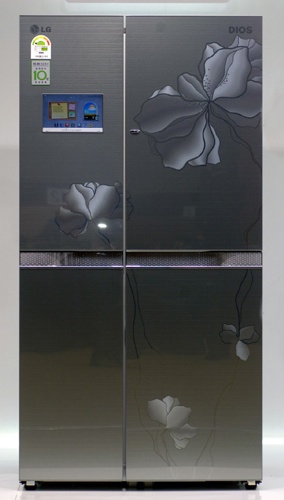
LG's net-connected refridgerator
Always find me in the kitchen at parties
While a fridge that automatically orders food might sound interesting, actually making one that works is fraught with difficulty. Many of the technologies used to work out what’s going in and out - RFID (Radio Frequency ID) chips, for example - make more sense in a warehouse than they do in a kitchen.
It’s simple to count the number of packets of sausages on a palette, for example, but RFID won’t tell you when some sneaky so-and-so's decided to put the box back in the fridge with just one left. Without widespread deployment of RFID, you’ll have to scan barcodes, effectively checking things in an out of the fridge like some bored shop-worker.
Even with RFID, unless you have sensors everywhere, how will the fridge know it’s milk, not water, that it’s weighing in a half-full bottle in the door-rack? What if you lie the bottle flat on the shelf? Will you remember to scan dry food you take from the cupboard as well?
And without a common online shopping API, what happens if the new fridge isn’t compatible with your supermarket?
