This article is more than 1 year old
Apple iMac 27in
Don’t try this at home, kids
Review For those of you who revel in Mac versus Windows shouting matches, click the Comments link now. You’ve already made up your minds, so feel free to dive into the debate without reading the review. That’s what you normally do, anyway.
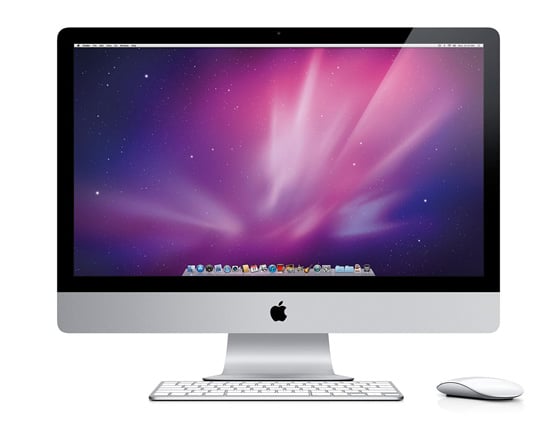
Widescreen viewing: Apple's iMac 27in
If you’re still with me, let me confirm the worst: Apple’s iMac range continues to be the most preposterously expensive series of home computers known to man. Towards the top-end, the 3.1GHz quad-core i5 edition with 27in display is one of the most pernicious offenders, setting you back in excess of £1,600 for the shallow glam of brushed aluminium, unnecessary space-age design and the kind of performance that’s wasted on its target domestic buyer. In other words, it’s god-damned gorgeous.
Now, before I go any further, there is a 3.4GHz quad core-i7 build-to-order model available, which, if you went with all the possible hardware extras (16GB RAM, SSD etc), would set you back in excess of £3k. Silliness aside, this review is of the off-the-shelf core i5 model.
Unpacking the product is a disquieting experience in itself. I try to imagine what it must be like to have splashed out your hard-earned, only for it to turn up in a slim box containing just four things: iMac, keyboard, mouse, power cable.

The Bluetooth keyboard lacks a numeric keypad, but retains the function keys
Despite its manageable 13.8kg, getting the unit out of the polystyrene and onto my desk is a potentially hernia-inducing task that might have been more safely achieved by two pairs of hands. And once I’ve stripped away the protective plastic, the depthless black of the 27in screen dominates my desk like the monolith at the foot of Dr Bowman’s deathbed.
