This article is more than 1 year old
Apple pulls app after dev publishes users' PINs
Too many folk use too-easy-to-guess passcodes
Is your phone PIN '1234'? If you're an iPhone owner, there's a good chance that it is. In fact, there's a good chance it's your PIN whatever handset you use.
iOS software developer Daniel Amitay, creator of an app called Big Brother Camera Security, added iPhone-style four-digit passcode access to his program. He was staggered to discover how many of them use codes that are easy to recall, but also very easy to guess.
Now, we'll overlook the moral implications of a developer covertly recording users' passcodes, even anonymously. Suffice it to say, Amitay has now had his nosy app yanked from the App Store. Amity says the iTunes EULA is on his side, but that's another story.
Amitay reasoned that punters will generally use the same code for his app as they will for their iPhone's main PIN lock - he says because the UIs are identical, but we'd suggest that the fundamental laziness of folk is also to blame - so he posted the most popular BBCS PINs.
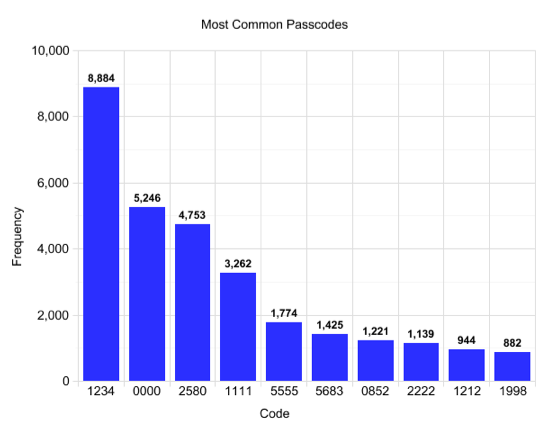
But what about those codes? Right after '1234' comes '0000', followed by '2580', '1111' and '5555'.
At sixth place is '5683' - an odd number until you realise it can be entered by tapping out the word 'love' on a mobile phone keypad.
Next comes '0852' - a vertical line upwards - '2222', '1212' and '1998'.
That last number is interesting: Amitay also found that years, from the 1990s and 2000s in particular, make very commonly used PINs.
Before some of you get all smug and suggest that Android users would never make such an elementary error of security, we're prepared to bet that they - and users of other phone operating systems too, from smartphones down to basic voice-centric units - will.
And, indeed, any other gadget or object - we're thinking credit and cash cards - that involve the use of a four-digit PIN.
At least we now have a list of numbers we know to avoid. Anyone who still uses '1234' after today really has no excuse. ®
