This article is more than 1 year old
Get your network ready for World IPv6 Day
Survey the lie of the LAN
Step 3 – Local setup
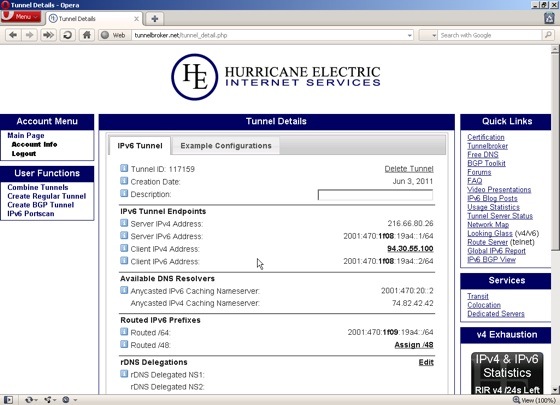
When the tunnel’s been created, you’ll see a summary screen showing the endpoints, with an IPv6 address for each end of the tunnel, as well as a routed /64, which you can use to assign IPv6 addresses to your own network. In the example here, you can see the client IPv6 address - my end of the tunnel - is 2001:470:1f08:19a4::2 and the prefix for my LAN is 2001:470:1f09:19a4. Note the difference in the third section of the address. The tunnel endpoints are using 1f08 and the local LAN uses 1f09.
You should also make a note of the IPv6 nameserver address. On some systems, this isn’t picked up automatically. For example, Mac OS X can auto-configure, but can’t pick up the DNS server address via DHCP6, so you’ll have to enter it manually in the Network preferences panel.
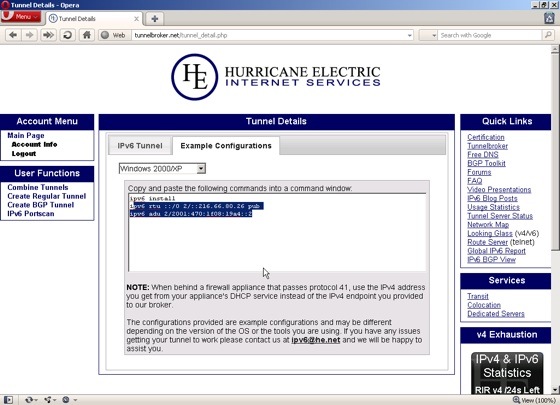
Once you’ve noted your specific addresses, click the Example configurations tab and select your operating system from the drop-down menu. You’ll see a list of commands that you need to copy and paste into a command window with administrator privileges. On Windows XP Pro this starts with the command:
ipv6 install
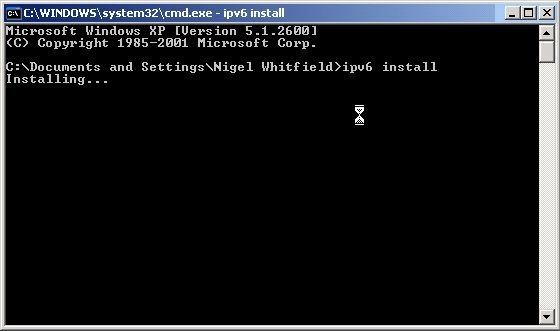
The next two commands – yes, that really is all there is to it – include the addresses for your system, so just copy and paste them one at a time from the example config on TunnelBroker. In theory, you can now head to IPv6 test site test-ipv6.com and you’ll receive confirmation that everything’s working correctly. That’s the theory. XP users may not always be so successful, thanks to Windows update KB978338, which is a hotfix designed to stop some potential security issues with IPv6 tunnelling, and has the side effect of breaking the setup on XP.
There are some workarounds – for example, some sites suggest adding an extra record to your DNS will fix it, as the fix uses that to check the tunnel is set up correctly. That didn’t work for me, and I used the alternative method of simply uninstalling KB978338. That’s not really recommended, though it solves the problem in the short term if you simply want to try things out using XP.