This article is more than 1 year old
Get your network ready for World IPv6 Day
Survey the lie of the LAN
Getting started
There’s a pretty good chance you’ll have everything you need to get IPv6 up and running – recent versions of Windows include the necessary software, so does Mac OS X, Linux and BSD.
You’ll probably need tweak the firewall on your router, to ensure that the tunnel can be passed through, and it’s worth stressing here that this effectively means that, as far as IPv6 goes, your system will be unprotected by the router. Consider the security implications of that carefully, especially if you’re going to connect other machines on your home network too.
I'm going to concentrate just on setup here – security is up to you.
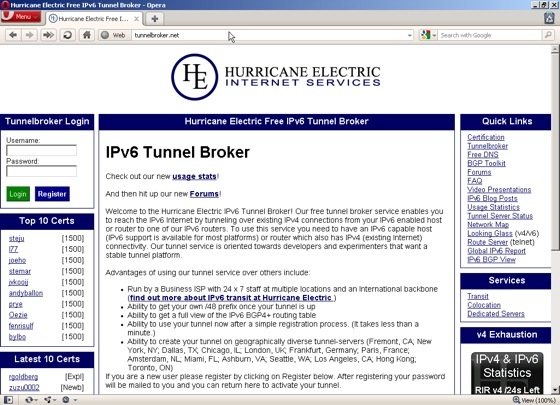
The other thing you’ll need is a tunnel service. In this example, I'm going to use Hurricane Electric’s Tunnel Broker, which is free and also provides an IPv6 DNS proxy, so you don’t really have to worry about setting up anything other than the tunnel itself.
I'm also using Windows XP Pro with SP3 for the first part of this example - the HE service provides configuration information for most common operating systems, so it’s easy to follow even if you are using a different platform.
Step 1 – Registration
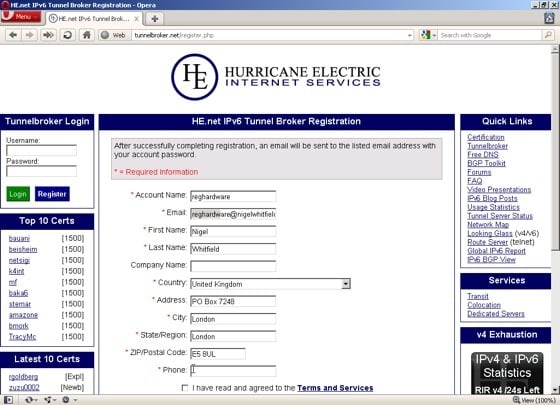
Fire up your web browser and head over to tunnelbroker.net, then click the Register button in the top left corner, fill in the form and wait for the confirmation email to be sent to you. When that arrives, head back to the site and sign in with the username you picked and the random password included in the email.