This article is more than 1 year old
Using the internet in the People's Republic of China
Our man reports from inside the Great Firewall
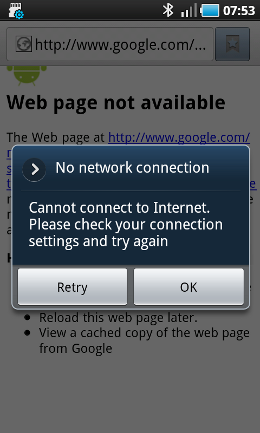
Your mobile data connection may be affected
After performing several such searches our cellular connection started playing up quite badly, dropping out at random and requiring a complete power cycle of the dongle before we could reconnect. There's no way to tell if that was down to our activities, or unrelated, but one did follow the other.
Tiananmen what?
China reckons that its site-blocking is no different than our own attempts to block sites hosting child pornography, albeit on a larger scale. But the comparison isn't really fair – at least not yet. We block child pornography because of the harm its production does to children, but moves are afoot to widen the UK's own firewall, and if that's allowed to happen then it becomes harder to attack China's on ideological grounds.
Using the internet in China you might never be aware of the blocking in place, and with a minimum of effort the visitor can participate in most online activities without significant impediment.
The decision to block services that can't be controlled, such as Twitter, has been enormously helpful to domestic versions and is increasingly looking like a trade barrier. In response to such an accusation the Chinese declare themselves happy to have Twitter locally just as soon as the company agrees to implement suitable censorship measures, and Facebook is rumoured to be about to launch a localised (and censored) version.
One could argue that using spurious national-security arguments to impose an unreasonable burden on foreign companies to the benefit of local competition is no different than what the US senators tried to do.
Had the congressmen succeeded in requiring operators to report all Huawei and ZTE kit used in critical locations, it would have been of a huge benefit to companies not in China. The difference, of course, is that the move failed, while in China domestic versions of Twitter and YouTube are thriving. ®
