This article is more than 1 year old
EU pay-by-tap accepts operator independence
GSMA not involved this time around
The European Payments Council guidelines for NFC proximity payments are up for debate, and this time the operator isn't considered an essential component though still the preferred partner.
In its last paper on the subject the EPC worked with operator-consortium The GSMA to work out how payment applications should be installed onto a secure element embedded in the operator's SIM, but this time a greater variety of options is presented and interested parties are invited to comment by June 17.
The proposal (117-page PDF/1.9 MB) addresses the thorny question of where the secure element should reside, and thus who controls it. The three popular options: SIM, embedded and SC Card, are presented and while the report still comes down on the side of the SIM it admits that "some business-related aspects ... might prove to be challenging".
The quickest solution to deploy, according to the EPC, is one which uses a secure element embedded in a microSD card. Such a solution allows the issuing bank to own the secure element, and if the microSD includes an NFC antenna and radio stack (such as those being built by Device Fidelity), then no other integration is required.
However, a secure element on a microSD has no secure way of interacting with the screen or keypad of the phone, and so cannot be sure that communications are not being intercepted until standards are forthcoming.
Which is what the EPC document is all about: deciding which standards should be adopted to facilitate communications between the surprisingly large number of parties involved in the proximity-payment ecosystem.
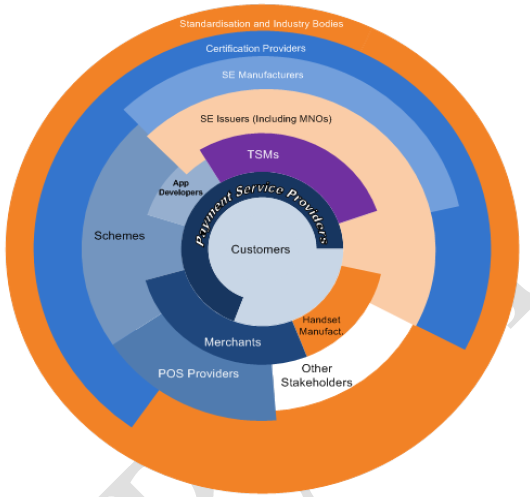
Note how the Mobile Network Operators (MNOs) are reduced to sitting in brackets
The document is aimed, primarily, at banks and payment processors, but it also highlights just how many parties intend to make money by facilitating proximity payments: quite possibly enough to threaten the viability of the whole idea. ®
