This article is more than 1 year old
Is there anything to find on bin Laden's hard drive?
Mining the 'mother lode' of intelligence
US officials are already referring to the trove of computer drives and disks seized from Osama bin Laden's compound as “the mother lode of intelligence.” Such gloating is probably premature.
As reported by Politico and others, the US Navy SEAL team that killed bin Laden on Sunday in Pakistan snatched computers, thumb drives and other electronic equipment. The gear has been sent to a secret location in Afghanistan where hundreds of intelligence officials are examining it.
“They cleaned it out,” one official boasted. “Can you imagine what's on Osama bin Laden's hard drive?”
It wouldn't be surprising for the answer to be: little, or very little.
As the world learned shortly after Sunday's lightning raid, bin Laden took extraordinary steps to hide his tracks from the countless spy agencies that worked day and night for 10 years to track him. He steadfastly shunned devices that left digital footprints. The huge compound where he died had no telephone or internet connection.
Given bin Laden's well-founded paranoia, he probably used encryption to prevent outsiders from reading the contents of his computer. And if that's the case, extracting intelligible data won't be nearly as straightforward as some reports suggest.
Probably the best chance intelligence officials have for recovering the data is exploiting implementation flaws in any encryption program bin Laden may have used. According to a 2007 report from the Middle East Media Research Institute, extremists with the Global Islamic Media Front released what was billed as “the first Islamic computer program for secure exchange [of information] on the Internet.”
It's unknown if bin Laden used “Mujahideen Secrets,” as the program is known, but if he did, that could be a huge boon for intelligence officials. Most successful attacks against encryption programs exploit implementation flaws, such as side channel vulnerabilities, in programs or algorithms that haven't been subjected to rigorous review from researchers.
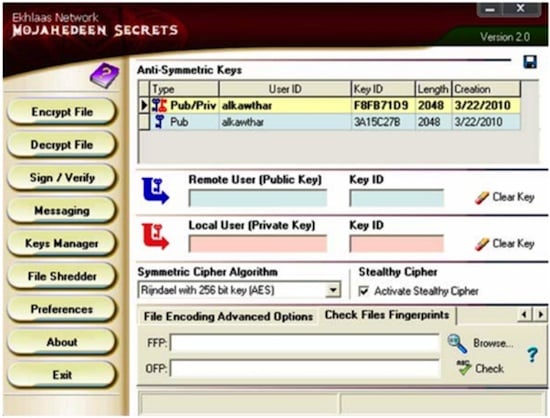
A screen shot of Mujahideen Secrets. The program was released in 2007 and updated the following year.
Mujahideen Secrets may offer 256-bit AES and 2048-bit asymmetrical encryption, but given the program's small and insular user base, it wouldn't be surprising if the software authors made crucial mistakes that even they don't know about.
It's more likely that bin Laden used a more reputable encryption program such as PGP or the open-source GnuPG. These programs, too, may have flaws known to US government spooks, but crypto experts generally say the likelihood they can be broken is smaller because, unlike less widely used programs, they have so far withstood robust scrutiny.
Assuming the encryption protecting bin Laden's secrets is sound, the government's best chance of recovering his data is to use forensics tools to find cleartext hidden in free space on the disks, said Nate Lawson, a cryptographer who is principal of security consultancy Root Labs . As The Reg pointed out in February, flash drives are dangerously hard to purge of data, making thumb drives a good starting point.
Lawson said intelligence personnel also might be able to brute-force the passphrase of bin Laden's encryption key. No one knows just how complex a passphrase the National Security Agency is capable of cracking. We're guessing it's considerable, but even that capability is limited and depending on the complexity of the phrase it could take time.
It will be interesting to learn just how adept bin Laden was at protecting the data stashed on his computer gear. It may turn out he made fatal mistakes encrypting it. Then again, don't be surprised if this intelligence mother lode is mostly filled with Fools Gold. ®
