This article is more than 1 year old
What now for the anti-piracy law?
ISPs 'hoist with their own petard' says judge
Analysis BT and TalkTalk threw the kitchen sink, legally speaking, at the Digital Economy Act and made very little stick.
Reading the ruling, you wonder why they bothered. High Court Judge Kenneth Parker summarised the DEA as "a more efficient, focussed and fair system than the current arrangements". Over and over, he pointed out that the Act didn't actually say what the objecting ISPs thought it said. He reaffirmed the right of ISPs to not become snoops, or comprise their "conduit" role. Any snooping is going to have to be carried out by copyright holders. And the DEA doesn't suddenly make them liable for damages.
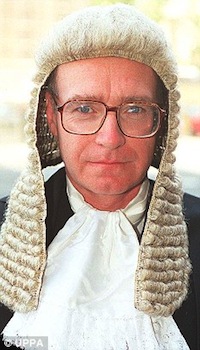
Parker gave BT and TalkTalk's lawyers a ticking off. At one point he found the ISPs' legal case so contradictory he said they'd hoisted themselves with their own petard. It wasn't the judge's role to favour one business interest over an other, he reminded them:
"It seems to me that if the Community legislator, as in this instance, has chosen specific language to give effect to a careful balancing of competing interests, the judge must be especially cautious before departing from the plain meaning of the text. To depart from that meaning creates the obvious risk of promoting the interest of one economic sector to the detriment of the other interested sector, and hence of seriously upsetting the balance between competing interests that the legislator has carefully struck," he notes.
The Act didn't actually say what technical sanctions (called "obligations") may eventually be introduced – and none may be. The technical obligations were "indicative, not exhaustive," the judge noted.
Nor did the DEA oblige the ISP to spy on users. "The role of the ISP under the DEA is essentially passive," he points out. The copyright holder must inform the ISP of specific suspected infringements, at which point the ISP must notify the user. It's no different to the role of the DVLC in giving out information identifying the owner of a number plate, said Parker.
Whether the Appeal for a Judicial Review was simply stalling or an expensive publicity stunt is a question that can only be answered by BT. They may wish to appeal, in which case it will drag on, but it's hard to see the EU Courts interpreting things very differently. The Act is sufficiently open-ended, and carefully worded, to see to that.
It's not all plain sailing from here, though.
The purpose of the Act isn't to make scapegoats out of hardcore infringers – who would dearly love to become martyrs for a day – and the determined, net-savvy user can bypass Torrent monitoring fairly easily.
Judge Parker acknowledged as much.
